!!! После завершения сканирования в Касперском и публикации отчета о сканировании: !!!
По логу FRST:
в системе остались поврежденные системные службы, которые надо исправить, и удалить службы созданные зловредом.
Скачайте с данной страницы
https://download.bleepingcomputer.com/win-services/windows-11-24H2/
следующие твики для исправления поврежденных служб:
BITS;
dosvc;
UsoSvc
WaaSMedicSvc
wuauserv
Запускаем каждый из загруженных файлов *.reg от имени Администратора, разрешаем внести изменения в реестр
Перезагружаем систему,
далее,
Выполните скрипт очистки в FRST
Запускаем FRST.exe от имени Администратора (если не запущен)
Копируем скрипт из браузера в буфер обмена, браузер закрываем.
Ждем, когда будет готов к работе,
Нажимаем в FRST кнопку «исправить».
Скрипт очистит систему, и завершит работу c перезагрузкой системы
Start::
S2 BITS_bkp; C:\WINDOWS\System32\qmgr.dll [1474560 2025-03-28] (Microsoft Windows -> Microsoft Corporation)
U2 dosvc_bkp; C:\WINDOWS\system32\dosvc.dll [98304 2025-03-27] (Microsoft Windows -> Microsoft Corporation)
S2 UsoSvc_bkp; C:\WINDOWS\system32\usosvc.dll [81920 2025-03-27] (Microsoft Windows -> Microsoft Corporation)
S3 WaaSMedicSvc_bkp; C:\WINDOWS\System32\WaaSMedicSvc.dll [94208 2025-03-27] (Microsoft Windows -> Microsoft Corporation)
S3 wuauserv_bkp; C:\Windows\system32\wuaueng.dll [3433472 2025-03-12] (Microsoft Windows -> Microsoft Corporation)
S3 wuauserv_bkp; C:\WINDOWS\system32\wuaueng.dll [181192 2025-03-28] (Microsoft Windows -> Корпорация Майкрософт)
Reboot::
End::
После перезагрузки:
Добавьте файл Fixlog.txt из папки, откуда запускали FRST, в ваше сообщение
Проверяем работоспособность системы.
Напишите по результату.
✔Advanced Anti-Malware Protection ✔Blocks Harmful Websites ✔Custom Malware Fixes Just For You
*Source of claim SH can remove it. Trial w/Credit card, no charge upfront; full terms.
Is Explorer.exe malicious? No, it is not. The legitimate Explorer.exe file is a secure system process developed by Microsoft for Windows operating systems. However, creators of malware, such as viruses, worms, and Trojans, intentionally use the same file name to evade detection.
Explorer.exe is a malicious computer program that uses disguise to enter its victims’ computers and then launch various harmful processes. Explorer.exe can be described as a Trojan horse virus that can be used differently depending on what the hackers controlling it are after.
Trojan horses have been around for a very long time and it is likely that all of this article’s readers have, at one point or another, heard about this infamous category of malware. However, not all Trojans are the same and while some could easily be detected by most antivirus programs, others, especially newer ones such as Explorer.exe, could silently infect any computer (even those protected by high-quality security programs) and conduct all sorts of harmful actions.
One of the key characteristics of this malware type is that its representatives are quite versatile and can be tasked with the completion of many different criminal goals. At the current moment, the information we have about Explorer.exe doesn’t allow us to confidently tell you the ultimate purpose of this threat, yet we can still give you an idea of what could be expected if this virus enters a given computer.
The Explorer.exe Virus
The versatility of the Trojan Horse viruses oftentimes makes them and the damage they could cause unpredictable, especially when the threat is as new as the Explorer.exe virus. Still, there are certain tendencies of how Trojans tend to be used.
SUMMARY:
Please follow all the steps below in order to remove Explorer.exe!
How to remove Explorer.exe
- First, click the Start Menu on your Windows PC.
- Type Programs and Settings in the Start Menu, click the first item, and find Explorer.exe in the programs list that would show up.
- Select Explorer.exe from the list and click on Uninstall.
- Follow the steps in the removal wizard.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide.
What we suggest you do first is, check the list of programs that are presently installed on the infected device and uninstall any rogue software that you find there:
- From the Start Menu, navigate to Control Panel ->>> Programs and Features ->>> Uninstall a Program.
- Next, carefully search for unfamiliar programs or programs that have been installed recently and could be related to Explorer.exe.
- If you find any of the programs suspicious then uninstall them if they turn out to be linked to Explorer.exe.
- If a notification appears on your screen when you try to uninstall a specific questionable program prompting you to just alter it or repair it, make sure you choose NO and complete the steps from the removal wizard.
Remove Explorer.exe from Chrome
- Click on the three dots in the right upper corner
- Go to more tools
- Now select extensions
- Remove the Explorer.exe extension
- Once you open Chrome, click on the three-dots icon to open the browser’s menu, go to More Tools/ More Options, and then to Extensions.
- Again, find the items on that page that could be linked to the malware and/or that might be causing problems in the browser and delete them.
- Afterwards, go to this folder: Computer > C: > Users > *Your User Account* > App Data > Local > Google > Chrome > User Data. In there, you will find a folder named Default – you should change its name to Backup Default and restart the PC.
- Note that the App Data folder is normally hidden so you’d have to first make the hidden files and folders on your PC visible before you can access it.
How to get rid of Explorer.exe on FF/Edge/etc.
- Open the browser and select the menu icon.
- From the menu, click on the Add-ons button.
- Look for the Explorer.exe extension
- Get rid of Explorer.exe by removing it from extensions
If using Firefox:
- Open Firefox
- Select the three parallel lines menu and go to Add-ons.
- Find the unwanted add-on and delete it from the browser – if there is more than one unwanted extension, remove all of them.
- Go to the browser menu again, select Options, and then click on Home from the sidebar to the left.
- Check the current addresses for the browser’s homepage and new-tab page and change them if they are currently set to address(es) you don’t know or trust.
If using MS Edge/IE:
- Start Edge
- Select the browser menu and go to Extensions.
- Find and uninstall any Edge extensions that look undesirable and unwanted.
- Select Settings from the browser menu and click on Appearance.
- Check the new-tab page address of the browser and if it has been modified by the malicious program or another unwanted app, change it to an address that you’d want to be the browser’s new-tab page.
How to Delete Explorer.exe
- Open task manager
- Look for the Explorer.exe process
- Select it and click on End task
- Open the file location to delete Explorer.exe
- Access the Task Manager by pressing together the Ctrl + Alt + Del keys and then selecting Task Manager.
- Open Processes and there try to find a process with the name of the unwanted software. If you find it, select it with the right button of the mouse and click on the Open File Location option.
- If you don’t see a malicious process in the Task Manager, look for another suspicious process with an unusual name. It is likely that the unwanted process would be using lots of RAM and CPU so pay attention to the number of resources each process is using.
- Tip: If you think you have singled out the unwanted process but are not sure, it’s always a good idea to search for information about it on the Internet – this should give you a general idea if the process is a legitimate one from a regular program or from your OS or if it is indeed likely linked to the adware.
- If you find another suspicious process, open its File Location too.
- Once in the File Location folder for the suspicious process, start testing all of the files that are stored there by dragging them to our free online scanner available below.
-
Each file will be scanned with up to 64 antivirus programs to ensure maximum accuracy
This scanner is free and will always remain free for our website’s users.
This file is not matched with any known malware in the database. You can either do a full real-time scan of the file or skip it to upload a new file. Doing a full scan with 64 antivirus programs can take up to 3-4 minutes per file.
Drag and Drop File Here To Scan
Analyzing 0 s
Each file will be scanned with up to 64 antivirus programs to ensure maximum accuracy
This scanner is based on VirusTotal’s API. By submitting data to it, you agree to their Terms of Service and Privacy Policy, and to the sharing of your sample submission with the security community. Please do not submit files with personal information if you do not want them to be shared.
- If the scanner finds malware in any of the files, return to the Processes tab in the Task Manager, select the suspected process, and then select the End Process option to quit it.
- Go back to the folder where the files of that process are located and delete all of the files that you are allowed to delete. If all files get deleted normally, exit the folder and delete that folder too. If one or more of the files showed an error message when you tried to delete them, leave them for now and return to try to delete them again once you’ve completed the rest of the guide.
How to Uninstall Explorer.exe
- Click on the home button
- Search for Startup Apps
- Look for Explorer.exe in there
- Uninstall Explorer.exe from Startup Apps by turning it off
- Now you need to carefully search for and uninstall any Explorer.exe-related entries from the Registry. The easiest way to do this is to open the Registry Editor app (type Regedit in the windows search field and press Enter) and then open a Find dialog (CTRL+F key combination) where you have to type the name of the threat.
- Perform a search by clicking on the Find Next button and delete any detected results. Do this as many times as needed until no more results are found.
- After that, to ensure that there are no remaining entries lined to Explorer.exe in the Registry, go manually to the following directories and delete them:
- HKEY_CURRENT_USER/Software/Random Directory.
- HKEY_CURRENT_USER/Software/Microsoft/Windows/CurrentVersion/Run/Random
- HKEY_CURRENT_USER/Software/Microsoft/Internet Explorer/Main/Random
What is Explorer.exe virus?
One particularly common way of using a Trojan virus is disguising the threat as a program many users would willingly download onto their computers. Once the user opens the disguised virus, the Trojan would demand Admin privileges and since the victim doesn’t know he or she is dealing with malware, they are likely to provide the requested privileges. After that, the virus would be free to do anything in the system. Usually, the access given to the malware is used for forcing the computer to carry out tasks such as Bitcoin mining for the hackers or spam email distribution. In those cases, the user is likely to notice the unwanted activities but they’d be powerless to stop them because the Trojan won’t allow it as long as it stays in the system. In most cases, such activities drain the computer’s resources and cause slow-downs, freezes, errors, and, in the more severe cases, BSOD crashes.
Is Explorer.exe virus dangerous?
Another common way Trojans are being used nowadays is to secretly deliver Ransomware to victims’ computers. In those cases, the Trojan plays a secondary role and the primary threat is the file-locking Ransomware.
Some Trojans , like Explorer.exe virus, Altruistic and PoSetup, are able to do spy on their victims. Any sensitive personal information gained by a Trojan could be used in harmful ways that could lead to various unforeseen consequences for the user.
These examples are only a small portion of all the possible things a Trojan could be used to complete. Even though we can’t tell you what Explorer.exe virus might do if it’s in your machine, we strongly advise you to not wait for the results of the infection. Instead, use the instructions we provide here and remove the threat before it has completed its agenda.
Brandon is a researcher and content creator in the fields of cyber-security and virtual privacy. Years of experience enable him to provide readers with important information and adequate solutions for the latest software and malware problems.
Brandon is a researcher and content creator in the fields of cyber-security and virtual privacy. Years of experience enable him to provide readers with important information and adequate solutions for the latest software and malware problems.
Explorer.exe is a malware computer virus designed to hide itself on the computer by resembling an Internet Explorer folder. The Explorer.exe folder needs to be removed from your computer as quickly as possible. If not, the virus file can wreak havoc on the system by damaging and corrupting important files in the Microsoft Windows system.
Step 1
Click the «Start» button in the lower left corner of the desktop. From the pull-up menu click «Run.» This loads a small search window with a single search bar.
Step 2
Type «Regedit» (without the quotation marks). The command opens the Windows Registry editor.
Step 3
Select the «HKEY_LOCAL_MACHINE» folder. A slew of other program files appears from this single file.
Step 4
Open the folder «Software» followed by «Microsoft,» then «Windows,» «CurrentVersion,» «Run,» «IEXPLORER»=»%System,» and select «iexplorer.exe.»
Step 5
Press the «delete» button and you are asked if you are sure you want to remove the file. Click «OK.»
Step 6
Open file «HKEY_CURRENT_USER» followed by «Software» and delete the folder «mmtest.»
Step 7
Close out the registry editor and restart the computer.
The real explorer.exe file is a safe Microsoft Windows system process, called “Windows Explorer”. Explorer.exe from Microsoft is an important part of the Windows operating system, however, criminals create malware such as viruses, worms, and Trojans deliberately give their processes the same file name to escape detection.
What is Explorer.exe process?
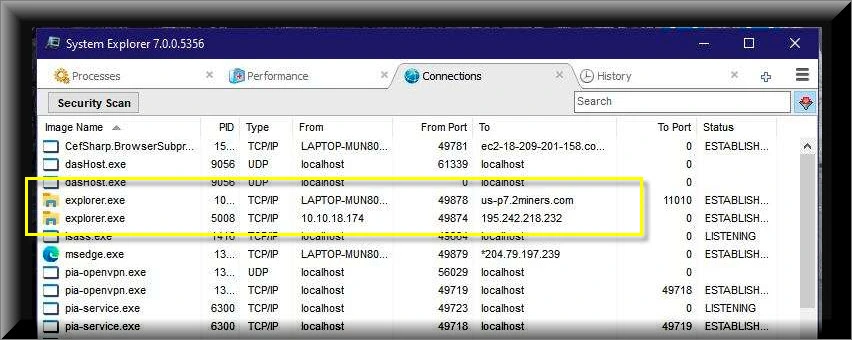
If your computer is very slow and there are multiple instances of Explorer.exe process running in Windows Task Manager, then your computer is infected with coin miner virus
The names of the executive file can be diverse, however, the consequences are generally identical. Since coin miners aim at cryptocurrency mining, they utilize all possible hardware power of your personal computer to run this process. This malware does not care about the fact that you probably want to make use of your device for other tasks – it will continuously consume over 80% of your processor power.
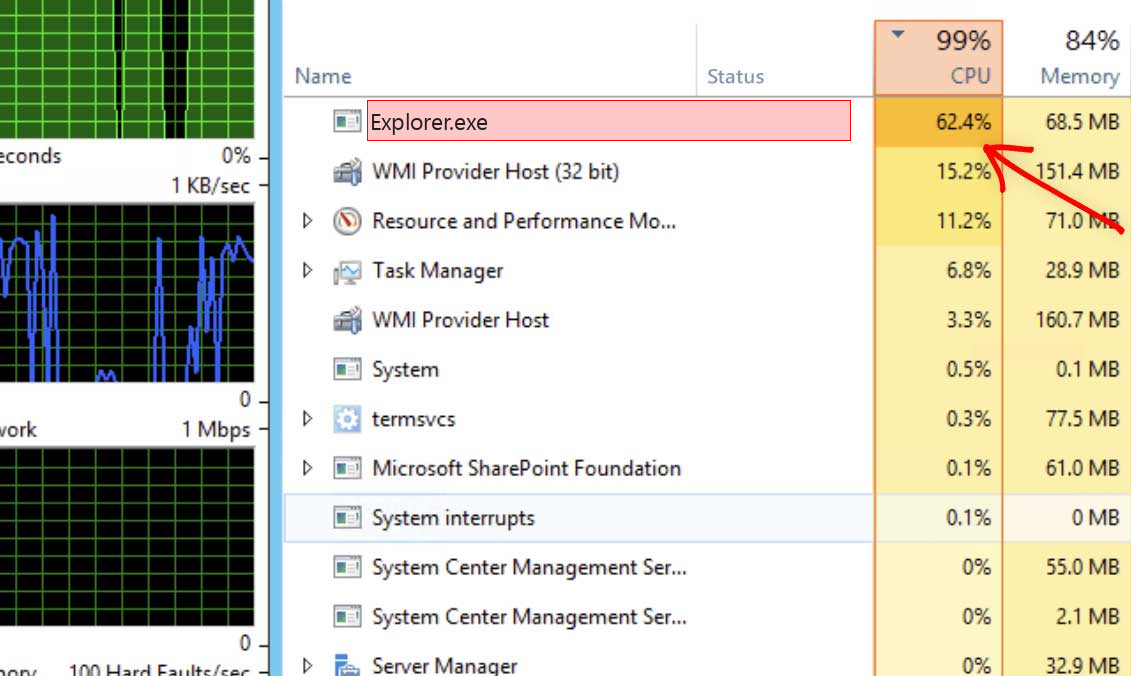
Explorer.exe – Extremely high CPU as well as GPU use
Besides CPU utilization, some of the coin miners additionally make use of GPU power for their operations. In that case, you will struggle even to see the mouse arrow moving – GPU is often utilized on 100%. It is not as important as CPU for system work, so Explorer.exe coin miner viruses do not waste time on trifles and utilize it all. It sometimes can result in sad consequences.
Shortly about cryptocurrency mining
Crypto mining is a term that means the activity of calculating the transaction block hash. That is an integral part of any project based on blockchain technology. Since this operation takes a lot of calculations, a very powerful computer is needed. Exactly, the GPU is better for this purpose, because they have more cores available. Cryptocurrency mining farms usually consist of tens and hundreds of graphic cards to conduct their activity effectively. Such computer systems are not usable for “general” purposes, like gaming or browsing the Web. Fraudsters who make a profit via this coin miner use someones’ PCs instead, even if they are used for regular activity.1
List of the typical coin miner symptoms
How dangerous is the Explorer.exe miner?
Coin miners does not deal damage to your files. However, they make a lot of unpleasant things with the whole system
Initially, Explorer.exe virus makes your computer overloaded. It is unable to run your applications now, as all processor power is consumed by malware. That malware does not care for your demands, all it focuses on is generating income on you. Even if you are patient, and you waited until the browser is open, you will likely struggle with extremely slow performance. Pages will open up for years, any kind of logins will likely take about a minute – just a headache for a person that does a job online.
Explorer.exe Technical Summary.
| File Name | Explorer.exe |
| Type | Trojan Coin Miner |
| Detection Name | Trojan:Win32/CoinMiner |
| Distribution Method | Software bundling, Intrusive advertisement, redirects to shady sites etc. |
| Similar behavior | Default.exe, St.exe, Xxx.exe |
| Removal | Download and install GridinSoft Anti-Malware for automatic Explorer.exe removal. |
“Visible” damage is not a solitary bad activity coin miners do to your computer. Explorer.exe coin miner additionally deals damage to your operating system. To complete all malevolent functions properly, it wrecks the security components of your system. You will likely see your Microsoft Defender disabled – malware stops it to avoid recognition. If you open the HOSTS file, you will likely see a number of new entries – they are added by this coin miner to connect your PC to a malicious mining network. All these adjustments shall be thrown back to the original in the process of system recovery.
Hardware effects of coin miner activity
Besides decreasing your PC’s performance, running at peak level for long times can cause damage to your device as well as increase power bills. Hardware elements are designed to easily get along with high load, but they are good with it only in case when they are in a good shape.
Tiny and covered CPU cooling system is quite hard to crack. Meanwhile, GPUs have big and easy-to-access rotors, which can be easily broken if touched while working, for example, by the user much before the virus injection. Malfunctioning cooling system, together with the unusually high load caused by Explorer.exe virus can easily lead to graphic card failure2. Video cards also tend to have very fast wear when used for cryptocurrency mining. It is likely an unwanted case when the performance of your video card plunges 20-30% only after 1-2 weeks of being exploited in such a way.
How did I get Explorer.exe coin miner virus?
Coin miners are spread through different ways, but their main sources are malicious banners and programs from dubious sources
Coin miners are one of the most common malicious programs among “major” viruses. Adware often acts as a carrier for Explorer.exe malware injection: it demonstrates to you the banners, which include a link to malware downloads. Sure, this abstract “malware” may belong to any kind – additional adware, spyware, rogue, or backdoor. But the statistics say that approximately 30% of all malware spread with the malevolent banners are coin miners – and Explorer.exe is just one of them.3
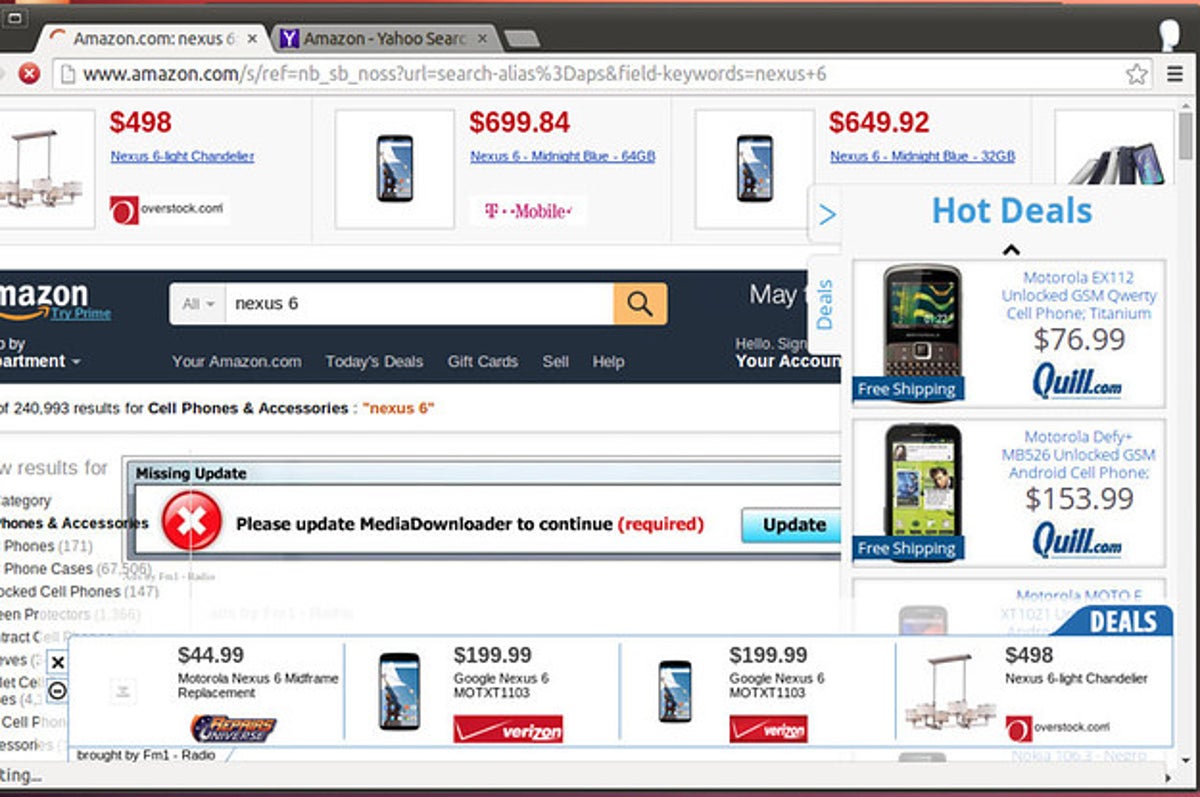
The example of malicious banners you can see in the Internet
Another way you could get this thing on your PC is by downloading it from the suspicious site as a part of a program. Users who spread hacked versions of well-known programs (which do not need the license key) have small chances to earn money. Therefore, there is a very big temptation to include malware in the final package of the hacked app and acquire a coin for every setup. Before criticizing these guys for hacking and also malware distribution, ask yourself – is it OK to avoid purchasing the program in this manner? It is much cheaper to pay $20-$30 one time than to pay a much greater sum for an antivirus program as well as new parts for your PC.
How to remove the Explorer.exe miner from my PC?
The best way to get rid of this coin miner virus is to use anti-malware software
Eliminating such a virus needs using special app. Effective security tools should have high performance at scanning and also be lightweight – in order to create no problems with utilization also on weak computers. Additionally, it is recommended to have proactive protection in your protection solution – to stop the virus even before it launches. Microsoft Defender lacks these elements for different reasons. That’s why I’d recommend you to use a third-party anti-malware program for that purpose. GridinSoft Anti-Malware is a great option that fits all of the mentioned features.4
Prior to the virus removal, it is important to boot your system into Safe Mode with Networking. Since Explorer.exe miner consumes a lot of CPU power, it is needed to stop it before launching the security program. Otherwise, your scan will last for years, even though the GridinSoft program is pretty lightweight.
Booting the PC into Safe Mode with Networking
Press the Start button, then choose Power, and click on Reboot while holding the Shift key on the keyboard.
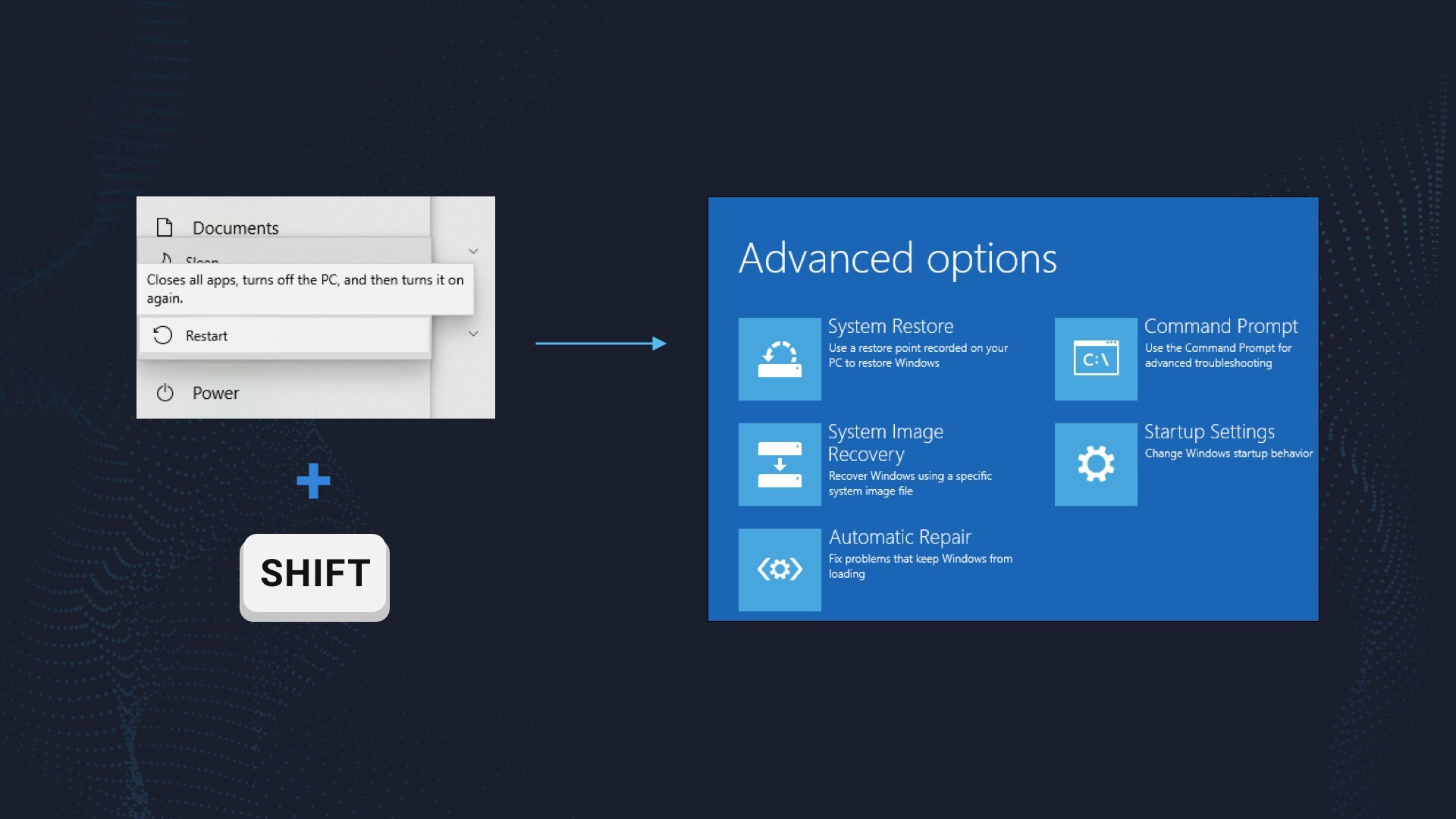
Windows will reboot into recovery mode. In that mode, choose Troubleshoot→ Startup Settings→ Safe Mode with Networking. Press the corresponding button on your keyboard to choose that option.
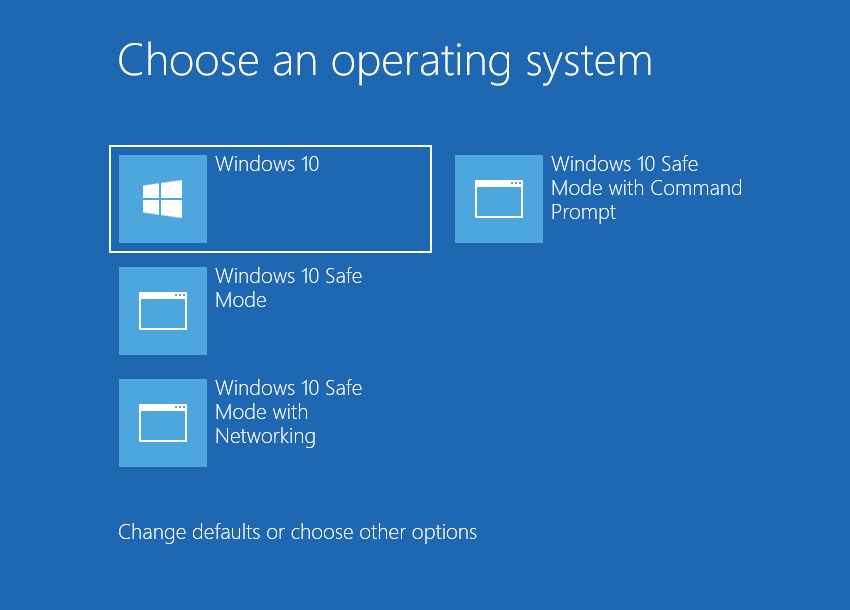
When your system is in Safe Mode, all third-party programs, just like the majority of non-crucial operating system components, are not launched with the system start. That gives you the ability to clean the PC without dealing with the high CPU usage of the coin miner.
Remove Explorer.exe coin miner virus with GridinSoft Anti-Malware
Download and install GridinSoft Anti-Malware. You can use this anti-malware program for free during its 6-day trial period. In that term, all functions are available, and it takes no payments to remove malware from your system.
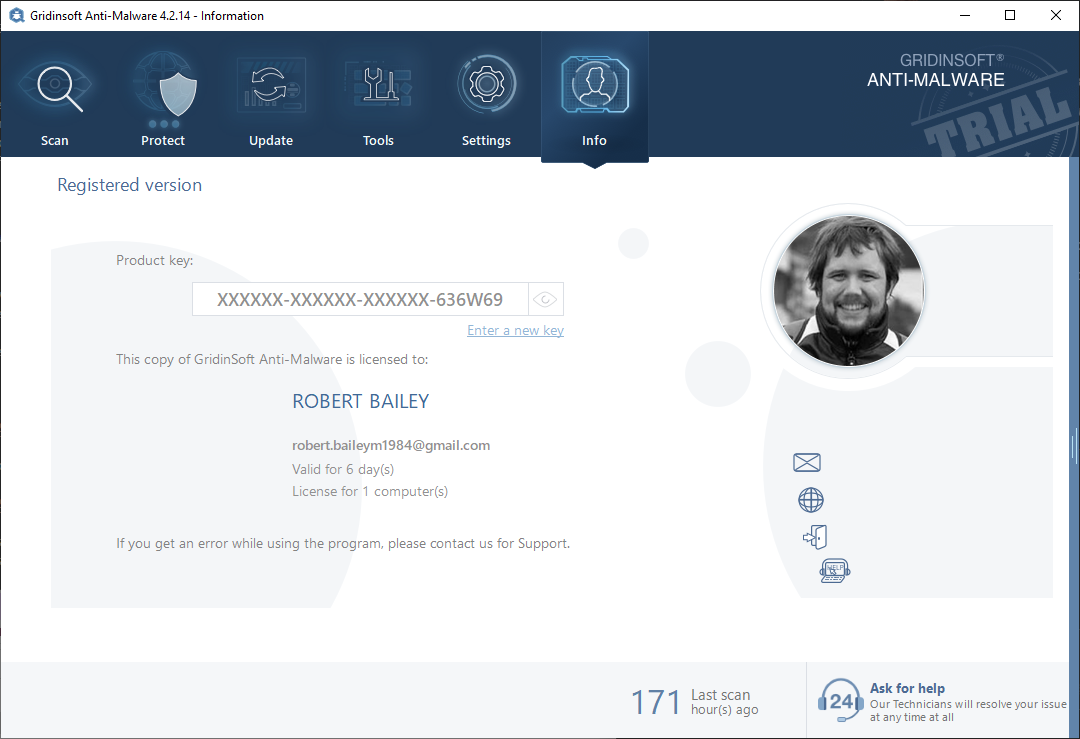
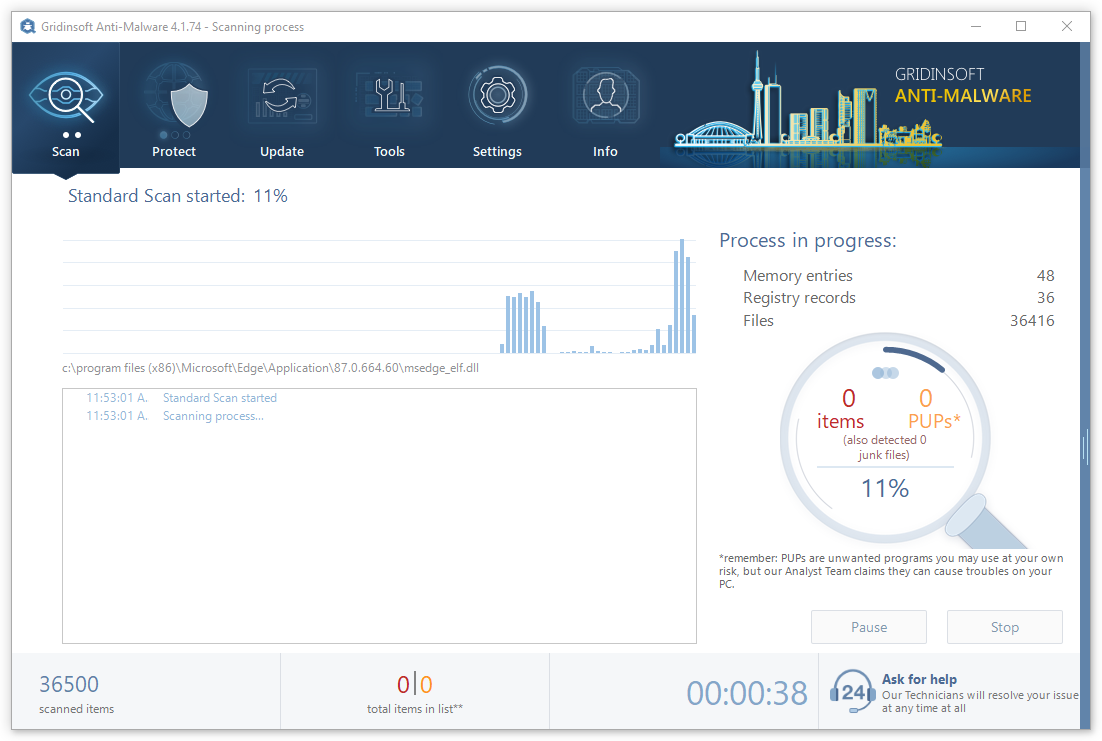
After activating your free trial, start Full scan. It may last up to 10 minutes. You may use the PC as usual.
When the scan is finished, press the Clean Now button to remove all detected elements from your system. This procedure takes less than a minute.
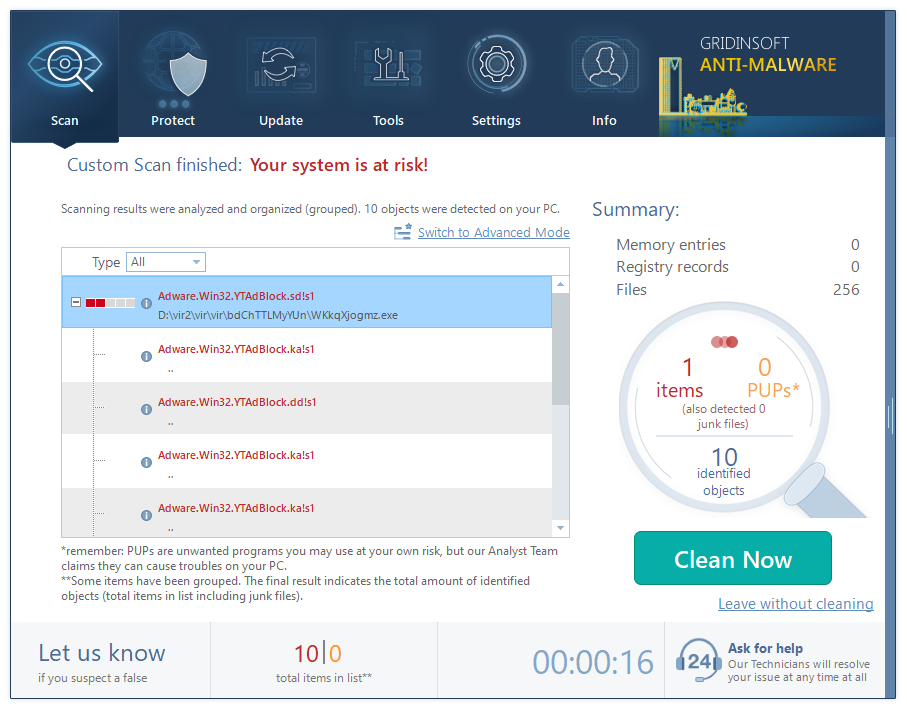
Now, you are good to go. Reboot your PC into a normal Windows mode and use just as there was nothing malicious.
Remove Explorer.exe Virus ⛏️ Trojan Coin Miner
Name: Explorer.exe
Description: The Explorer.exe is a Trojan Coin Miner that uses the infected computer’s sources to mine electronic money without your authorization. This Explorer.exe will create your CPU to go for very warm temperatures for prolonged periods of time, which could reduce the life of the CPU.
Operating System: Windows
Application Category: Trojan
References
- Detailed explanation of how does crypto mining work.
- About unwanted effects for GPUs in the process of crypto mining.
- Read more about various malware type on Cybersecurity Glossary.
- Our review on GridinSoft Anti-Malware.
Spanish Turkish
