
In this chapter, I will explain how to create openssl.conf file with the way that Windows can process it.
Parts to be changed in the default openssl.conf:
For creating a default openssl.conf, Jamie’s amazing article would be a good start point.
There are many differences between original Windows certificates and those created with using OpenSSL on Linux:
Difference 1 → Issuer:
Issuer is one of the most important field in the certificates. This must be interpreted correctly in order to make Windows accept our handcrafted certificate.
Difference between certificate created with default openssl.conf and original Windows certificate:

Solution for Difference 1:
In this part, we define the section for the req command.
We can edit default_bits, default_md parts. But most importantly, we can change how to form the DN with editing the req_distinguished_name section.
Default [ req ] part would be similar to:
[ req ]
default_bits = 2048
distinguished_name = req_distinguished_name
string_mask = utf8only
default_md = sha256
x509_extensions = v3_ca
Enter fullscreen mode
Exit fullscreen mode
Corresponding default [ req_distinguished_name ] :
[ req_distinguished_name ]
# See <https://en.wikipedia.org/wiki/Certificate_signing_request>.
countryName = Country Name (2 letter code)
stateOrProvinceName = State or Province Name
localityName = Locality Name
0.organizationName = Organization Name
organizationalUnitName = Organizational Unit Name
commonName = Common Name
emailAddress = Email Address
Enter fullscreen mode
Exit fullscreen mode
As you can see, there are lots of fields like countryName, stateOrProvinceName, localityName…
This is why we see lots of information in the ‘Issuer’ field of the certificates created with OpenSSL.
Edited [ req_distinguished_name ] should be similar to:
[ req_distinguished_name ]
1.DC = com
0.DC = company
DC = subdomain
commonName = Common Name
Enter fullscreen mode
Exit fullscreen mode
And user should type in that order:
As a result, we successfully created a valid issuer:
Difference 2 → Missing Fields:
Two fields, «Certificate Template Name» and «CA Version», are not available on the certificate that created with OpenSSL on Linux.
It is hard to know about which fields are precisely checked when tricking Windows to accept your handcrafted OpenSSL certificate, but I think it is a good practice to make your certificate look exactly like the original one.

Solution for Difference 2:
Firstly, define OID’s at the top of our openssl.conf file:
oid_section = OIDs
[ OIDs ]
certificateTemplateName = 1.3.6.1.4.1.311.20.2
caVersion = 1.3.6.1.4.1.311.21.1
Enter fullscreen mode
Exit fullscreen mode
We can skip the definition of the OID’s and use the OID directly, of course. But defining them first and using them as variables would be a good practice.
Secondly, create a new requirement in [ reg ], let’s say v3_req :
[ req ]
default_bits = 2048
distinguished_name = req_distinguished_name
string_mask = default
default_md = sha256
x509_extensions = v3_ca
req_extensions = v3_req
Enter fullscreen mode
Exit fullscreen mode
Lastly, define [ v3_req ] :
[ v3_req ]
subjectKeyIdentifier = hash
basicConstraints = critical, CA:true
keyUsage = digitalSignature, cRLSign, keyCertSign
certificateTemplateName = ASN1:PRINTABLESTRING:CA
caVersion = ASN1:INTEGER:0
Enter fullscreen mode
Exit fullscreen mode
After that, you should create your certificate with the following parameter:
-extensions v3_req
Enter fullscreen mode
Exit fullscreen mode
As a result, we successfully created our certificate fields:

Final:
We have successfully created our openssl.conf!
You can view the whole openssl.conf file from: GitHub Gist

NAME¶
config — OpenSSL CONF library configuration files
DESCRIPTION¶
This page documents the syntax of OpenSSL configuration files, as parsed by NCONF_load(3) and related functions. This format is used by many of the OpenSSL commands, and to initialize the libraries when used by any application.
The first part describes the general syntax of the configuration files, and subsequent sections describe the semantics of individual modules. Other modules are described in fips_config(5) and x509v3_config(5). The syntax for defining ASN.1 values is described in ASN1_generate_nconf(3).
SYNTAX¶
A configuration file is a series of lines. Blank lines, and whitespace between the elements of a line, have no significance. A comment starts with a # character; the rest of the line is ignored. If the # is the first non-space character in a line, the entire line is ignored.
Directives¶
Two directives can be used to control the parsing of configuration files: .include and .pragma.
For compatibility with older versions of OpenSSL, an equal sign after the directive will be ignored. Older versions will treat it as an assignment, so care should be taken if the difference in semantics is important.
A file can include other files using the include syntax:
If pathname is a simple filename, that file is included directly at that point. Included files can have .include statements that specify other files. If pathname is a directory, all files within that directory that have a .cnf or .conf extension will be included. (This is only available on systems with POSIX IO support.) Any sub-directories found inside the pathname are ignored. Similarly, if a file is opened while scanning a directory, and that file has an .include directive that specifies a directory, that is also ignored.
As a general rule, the pathname should be an absolute path; this can be enforced with the abspath and includedir pragmas, described below. The environment variable OPENSSL_CONF_INCLUDE, if it exists, is prepended to all relative pathnames. If the pathname is still relative, it is interpreted based on the current working directory.
To require all file inclusions to name absolute paths, use the following directive:
.pragma [=] abspath:value
The default behavior, where the value is false or off, is to allow relative paths. To require all .include pathnames to be absolute paths, use a value of true or on.
In these files, the dollar sign, $, is used to reference a variable, as described below. On some platforms, however, it is common to treat $ as a regular character in symbol names. Supporting this behavior can be done with the following directive:
.pragma [=] dollarid:value
The default behavior, where the value is false or off, is to treat the dollarsign as indicating a variable name; foo$bar is interpreted as foo followed by the expansion of the variable bar. If value is true or on, then foo$bar is a single seven-character name and variable expansions must be specified using braces or parentheses.
.pragma [=] includedir:value
If a relative pathname is specified in the .include directive, and the OPENSSL_CONF_INCLUDE environment variable doesn’t exist, then the value of the includedir pragma, if it exists, is prepended to the pathname.
Settings¶
A configuration file is divided into a number of sections. A section begins with the section name in square brackets, and ends when a new section starts, or at the end of the file. The section name can consist of alphanumeric characters and underscores. Whitespace between the name and the brackets is removed.
The first section of a configuration file is special and is referred to as the default section. This section is usually unnamed and spans from the start of file until the first named section. When a name is being looked up, it is first looked up in the current or named section, and then the default section if necessary.
The environment is mapped onto a section called ENV.
Within a section are a series of name/value assignments, described in more detail below. As a reminder, the square brackets shown in this example are required, not optional:
[ section ]
name1 = This is value1
name2 = Another value
...
[ newsection ]
name1 = New value1
name3 = Value 3
The name can contain any alphanumeric characters as well as a few punctuation symbols such as . , ; and _. Whitespace after the name and before the equal sign is ignored.
If a name is repeated in the same section, then all but the last value are ignored. In certain circumstances, such as with Certificate DNs, the same field may occur multiple times. In order to support this, commands like openssl-req(1) ignore any leading text that is preceded with a period. For example:
1.OU = First OU
2.OU = Second OU
The value consists of the string following the = character until end of line with any leading and trailing whitespace removed.
The value string undergoes variable expansion. The text $var or ${var} inserts the value of the named variable from the current section. To use a value from another section use $section::name or ${section::name}. By using $ENV::name, the value of the specified environment variable will be substituted.
Variables must be defined before their value is referenced, otherwise an error is flagged and the file will not load. This can be worked around by specifying a default value in the default section before the variable is used.
Any name/value settings in an ENV section are available to the configuration file, but are not propagated to the environment.
It is an error if the value ends up longer than 64k.
It is possible to escape certain characters by using a single ‘ or double « quote around the value, or using a backslash \ before the character, By making the last character of a line a \ a value string can be spread across multiple lines. In addition the sequences \n, \r, \b and \t are recognized.
The expansion and escape rules as described above that apply to value also apply to the pathname of the .include directive.
OPENSSL LIBRARY CONFIGURATION¶
The sections below use the informal term module to refer to a part of the OpenSSL functionality. This is not the same as the formal term FIPS module, for example.
The OpenSSL configuration looks up the value of openssl_conf in the default section and takes that as the name of a section that specifies how to configure any modules in the library. It is not an error to leave any module in its default configuration. An application can specify a different name by calling CONF_modules_load_file(), for example, directly.
OpenSSL also looks up the value of config_diagnostics. If this exists and has a nonzero numeric value, any error suppressing flags passed to CONF_modules_load() will be ignored. This is useful for diagnosing misconfigurations but its use in production requires additional consideration. With this option enabled, a configuration error will completely prevent access to a service. Without this option and in the presence of a configuration error, access will be allowed but the desired configuration will not be used.
# These must be in the default section
config_diagnostics = 1
openssl_conf = openssl_init
[openssl_init]
oid_section = oids
providers = providers
alg_section = evp_properties
ssl_conf = ssl_configuration
engines = engines
random = random
[oids]
... new oids here ...
[providers]
... provider stuff here ...
[evp_properties]
... EVP properties here ...
[ssl_configuration]
... SSL/TLS configuration properties here ...
[engines]
... engine properties here ...
[random]
... random properties here ...
The semantics of each module are described below. The phrase «in the initialization section» refers to the section identified by the openssl_conf or other name (given as openssl_init in the example above). The examples below assume the configuration above is used to specify the individual sections.
ASN.1 Object Identifier Configuration¶
The name oid_section in the initialization section names the section containing name/value pairs of OID’s. The name is the short name; the value is an optional long name followed by a comma, and the numeric value. While some OpenSSL commands have their own section for specifying OID’s, this section makes them available to all commands and applications.
[oids]
shortName = a very long OID name, 1.2.3.4
newoid1 = 1.2.3.4.1
some_other_oid = 1.2.3.5
If a full configuration with the above fragment is in the file example.cnf, then the following command line:
OPENSSL_CONF=example.cnf openssl asn1parse -genstr OID:1.2.3.4.1
will output:
0:d=0 hl=2 l= 4 prim: OBJECT :newoid1
showing that the OID «newoid1» has been added as «1.2.3.4.1».
Provider Configuration¶
The name providers in the initialization section names the section containing cryptographic provider configuration. The name/value assignments in this section each name a provider, and point to the configuration section for that provider. The provider-specific section is used to specify how to load the module, activate it, and set other parameters.
Within a provider section, the following names have meaning:
-
identity
This is used to specify an alternate name, overriding the default name specified in the list of providers. For example:
[providers] foo = foo_provider [foo_provider] identity = my_fips_module -
module
Specifies the pathname of the module (typically a shared library) to load.
-
activate
If present and set to one of the values yes, on, true or 1, then the associated provider will be activated. Conversely, setting this value to no, off, false, or 0 will prevent the provider from being activated. Settings can be given in lower or uppercase. Setting activate to any other setting, or omitting a setting value will result in an error.
= item soft_load
If enabled, informs the library to clear the error stack on failure to activate requested provider. A value of 1, yes, true or on (in lower or uppercase) will activate this setting, while a value of 0, no, false, or off (again in lower or uppercase) will disable this setting. Any other value will produce an error. Note this setting defaults to off if not provided
All parameters in the section as well as sub-sections are made available to the provider.
Default provider and its activation¶
If no providers are activated explicitly, the default one is activated implicitly. See OSSL_PROVIDER-default(7) for more details.
If you add a section explicitly activating any other provider(s), you most probably need to explicitly activate the default provider, otherwise it becomes unavailable in openssl. It may make the system remotely unavailable.
EVP Configuration¶
The name alg_section in the initialization section names the section containing algorithmic properties when using the EVP API.
Within the algorithm properties section, the following names have meaning:
-
default_properties
The value may be anything that is acceptable as a property query string for EVP_set_default_properties().
-
fips_mode (deprecated)
The value is a boolean that can be yes or no. If the value is yes, this is exactly equivalent to:
default_properties = fips=yesIf the value is no, nothing happens. Using this name is deprecated, and if used, it must be the only name in the section.
SSL Configuration¶
The name ssl_conf in the initialization section names the section containing the list of SSL/TLS configurations. As with the providers, each name in this section identifies a section with the configuration for that name. For example:
[ssl_configuration]
server = server_tls_config
client = client_tls_config
system_default = tls_system_default
[server_tls_config]
... configuration for SSL/TLS servers ...
[client_tls_config]
... configuration for SSL/TLS clients ...
The configuration name system_default has a special meaning. If it exists, it is applied whenever an SSL_CTX object is created. For example, to impose system-wide minimum TLS and DTLS protocol versions:
[tls_system_default]
MinProtocol = TLSv1.2
MinProtocol = DTLSv1.2
The minimum TLS protocol is applied to SSL_CTX objects that are TLS-based, and the minimum DTLS protocol to those are DTLS-based. The same applies also to maximum versions set with MaxProtocol.
Each configuration section consists of name/value pairs that are parsed by SSL_CONF_cmd(3), which will be called by SSL_CTX_config() or SSL_config(), appropriately. Note that any characters before an initial dot in the configuration section are ignored, so that the same command can be used multiple times. This probably is most useful for loading different key types, as shown here:
[server_tls_config]
RSA.Certificate = server-rsa.pem
ECDSA.Certificate = server-ecdsa.pem
Engine Configuration¶
The name engines in the initialization section names the section containing the list of ENGINE configurations. As with the providers, each name in this section identifies an engine with the configuration for that engine. The engine-specific section is used to specify how to load the engine, activate it, and set other parameters.
Within an engine section, the following names have meaning:
-
engine_id
This is used to specify an alternate name, overriding the default name specified in the list of engines. If present, it must be first. For example:
[engines] foo = foo_engine [foo_engine] engine_id = myfoo -
dynamic_path
This loads and adds an ENGINE from the given path. It is equivalent to sending the ctrls SO_PATH with the path argument followed by LIST_ADD with value 2 and LOAD to the dynamic ENGINE. If this is not the required behaviour then alternative ctrls can be sent directly to the dynamic ENGINE using ctrl commands.
-
init
This specifies whether to initialize the ENGINE. If the value is 0 the ENGINE will not be initialized, if the value is 1 an attempt is made to initialize the ENGINE immediately. If the init command is not present then an attempt will be made to initialize the ENGINE after all commands in its section have been processed.
-
default_algorithms
This sets the default algorithms an ENGINE will supply using the function ENGINE_set_default_string().
All other names are taken to be the name of a ctrl command that is sent to the ENGINE, and the value is the argument passed with the command. The special value EMPTY means no value is sent with the command. For example:
[engines]
foo = foo_engine
[foo_engine]
dynamic_path = /some/path/fooengine.so
some_ctrl = some_value
default_algorithms = ALL
other_ctrl = EMPTY
Random Configuration¶
The name random in the initialization section names the section containing the random number generator settings.
Within the random section, the following names have meaning:
-
random
This is used to specify the random bit generator. For example:
[random] random = CTR-DRBGThe available random bit generators are:
- CTR-DRBG
- HASH-DRBG
- HMAC-DRBG
-
cipher
This specifies what cipher a CTR-DRBG random bit generator will use. Other random bit generators ignore this name. The default value is AES-256-CTR.
-
digest
This specifies what digest the HASH-DRBG or HMAC-DRBG random bit generators will use. Other random bit generators ignore this name.
-
properties
This sets the property query used when fetching the random bit generator and any underlying algorithms.
-
seed
This sets the randomness source that should be used. By default SEED-SRC will be used outside of the FIPS provider. The FIPS provider uses call backs to access the same randomness sources from outside the validated boundary.
-
seed_properties
This sets the property query used when fetching the randomness source.
-
random_provider
This sets the provider to use for the RAND_bytes(3) calls instead of the built-in entropy sources. It defaults to «fips». If the named provider is not loaded, the built-in entropy sources will be used.
EXAMPLES¶
This example shows how to use quoting and escaping.
# This is the default section.
HOME = /temp
configdir = $ENV::HOME/config
[ section_one ]
# Quotes permit leading and trailing whitespace
any = " any variable name "
other = A string that can \
cover several lines \
by including \\ characters
message = Hello World\n
[ section_two ]
greeting = $section_one::message
This example shows how to expand environment variables safely. In this example, the variable tempfile is intended to refer to a temporary file, and the environment variable TEMP or TMP, if present, specify the directory where the file should be put. Since the default section is checked if a variable does not exist, it is possible to set TMP to default to /tmp, and TEMP to default to TMP.
# These two lines must be in the default section.
TMP = /tmp
TEMP = $ENV::TMP
# This can be used anywhere
tmpfile = ${ENV::TEMP}/tmp.filename
This example shows how to enforce FIPS mode for the application sample.
sample = fips_config
[fips_config]
alg_section = evp_properties
[evp_properties]
default_properties = "fips=yes"
ENVIRONMENT¶
-
OPENSSL_CONF
The path to the config file, or the empty string for none. Ignored in set-user-ID and set-group-ID programs.
-
OPENSSL_ENGINES
The path to the engines directory. Ignored in set-user-ID and set-group-ID programs.
-
OPENSSL_MODULES
The path to the directory with OpenSSL modules, such as providers. Ignored in set-user-ID and set-group-ID programs.
-
OPENSSL_CONF_INCLUDE
The optional path to prepend to all .include paths.
BUGS¶
There is no way to include characters using the octal \nnn form. Strings are all null terminated so nulls cannot form part of the value.
The escaping isn’t quite right: if you want to use sequences like \n you can’t use any quote escaping on the same line.
The limit that only one directory can be opened and read at a time can be considered a bug and should be fixed.
HISTORY¶
An undocumented API, NCONF_WIN32(), used a slightly different set of parsing rules there were intended to be tailored to the Microsoft Windows platform. Specifically, the backslash character was not an escape character and could be used in pathnames, only the double-quote character was recognized, and comments began with a semi-colon. This function was deprecated in OpenSSL 3.0; applications with configuration files using that syntax will have to be modified.
SEE ALSO¶
openssl-x509(1), openssl-req(1), openssl-ca(1), openssl-fipsinstall(1), ASN1_generate_nconf(3), EVP_set_default_properties(3), CONF_modules_load(3), CONF_modules_load_file(3), RAND_bytes(3), fips_config(5), and x509v3_config(5).
COPYRIGHT¶
Copyright 2000-2025 The OpenSSL Project Authors. All Rights Reserved.
Licensed under the Apache License 2.0 (the «License»). You may not use this file except in compliance with the License. You can obtain a copy in the file LICENSE in the source distribution or at https://www.openssl.org/source/license.html.
- Home
- Blog
-
Step-By-Step Procedure to Install OpenSSL on a Windows Machine
/
/

OpenSSL is an open-source cryptographic library that provides a robust toolkit for securing communications and creating, managing, and verifying digital certificates. It is widely used for implementing Secure Sockets Layer (SSL) and Transport Layer Security (TLS) protocols to encrypt connections between clients and servers.
Some of the common uses of OpenSSL include setting up private certificate authorities, generating public/private key pairs, creating certificate signing requests, exporting private key from certificates, converting between certificate formats like PEM and PFX, validating SSL connections, and more.
In this comprehensive guide, we will cover how to download, install, and configure OpenSSL on Windows machines. While Linux distributions come with OpenSSL pre-installed, Windows users need to manually install OpenSSL by getting the binaries from trusted third-party sources.
We will go over the prerequisites, walk through the installation steps, explain how to set up environment variables, and verify the installation to ensure OpenSSL is ready to use on your Windows PC or server. Whether you are a developer, IT admin, or security professional, this step-by-step procedure will help you get OpenSSL running smoothly on your Windows systems.
What is OpenSSL and Why Should We Install OpenSSL on a Windows PC?
OpenSSL is an open-source cryptographic library that provides a robust toolkit for securing communications and applications. Though primarily used on Linux, installing OpenSSL on Windows unlocks powerful capabilities. OpenSSL is mostly for system administrators, developers, and Windows users who wants to implement SSL/TLS connections in their apps and scripts. It enables generating X.509 certificates and certificate signing requests (CSRs) for securing websites and internal infrastructure. Developers can call OpenSSL crypto functions to encrypt data and implement PKI authentication in their apps.
System administrators can manage certificates, test secure connections, and integrate OpenSSL into automation scripts. OpenSSL also helps troubleshoot connection issues by analyzing network traffic and certificates.
There are a lot of things you can do using OpenSSL. Only a few of them are listed here:
-
You can create your own Certificate Authority and issue certificates on your network.
-
Convert digital certificates from one to another format.
-
Export or Import private keys from the certificates.
-
Validate the HTTPS connections to the destination website.
-
Verify the certificate of the destination website.
-
Run benchmark tests of your server and remote website.
-
Extract information like issuer, subject, issued and expiring dates, and fingerprint from certificates.
-
Create CSR.
-
Decode CSR and Certificates to verify contents.
You can enjoy the features of OpenSSL if you have installed it on your Windows machine. Before we begin the procedure to install OpenSSL on the Windows platform, let’s see the prerequisites.
Download OpenSSL Installer for Windows
Before we jump into the installation of OpenSSL on a Windows PC, let’s cover a few things about the Linux package. As we said in the introduction, OpenSSL will come as part of default installation packages in all the popular Linux distributions, even if you need a specific version of OpenSSL for your Linux machine, you can download the source code of OpenSSL on from its official website alternatively from here and compel it on Linux.
Well, If you are looking to download the OpenSSL package for your Windows machine from its official website, you can’t. It’s because OpenSSL doesn’t release official OpenSSL installers for Windows. You should depend on a few third-party distributors who distribute OpenSSL installer files for Windows platforms. OpenSSL has published the list of all trusted third-party distributors on its Wiki page. Please download and install only from these listed third-party sites.
Disclaimer Message from OpenSSL: The listing of these third-party products does not imply any endorsement by the OpenSSL project, and these organizations are not affiliated in any way with OpenSSL other than by reference to their independent websites here. In particular, any donations or payments to any of these organizations will not be known to, seen by, or in any way benefit the OpenSSL project.
– OpenSSL
Note: OpenSSL says none of these vendors are partnered with OpenSSL, so issues with these installers should be directly communicated with the distributors. OpenSSL doesn’t hold any responsibilities for these installers. Use these OpenSSL-derived products at your own risk; these products have not been evaluated or tested by the OpenSSL project.
List of Third-Party OpenSSL Distributions:
| Product | Description | URL |
|---|---|---|
| OpenSSL for Web (using WebAssembly) | OpenSSL 3.0 ported to WebAssembly (in October 2021). Uses Emscripten and xterm.js to emulate a terminal in your browser. WASI binaries are supported too. The Wasm execution happens using WebWorkers if the browser supports them. Originally developed for the cryptology playground “CrypTool-Online”. Code is open-source on GitHub. | OpenSSL-React app: https://github.com/cryptool-org/openssl-webtermBasic Wasm terminal: https://github.com/cryptool-org/wasm-webtermRunning sample: https://www.cryptool.org/en/cto/openssl |
| OpenSSL for Windows | Works with MSVC++, Builder 3/4/5, and MinGW. Comes in form of self-install executables. | https://slproweb.com/products/Win32OpenSSL.html |
| OpenSSL for Windows | Pre-compiled Win32/64 libraries without external dependencies to the Microsoft Visual Studio Runtime DLLs, except for the system provided msvcrt.dll. | https://indy.fulgan.com/SSL/ |
| OpenSSL for Windows | Reproducible builds with latest MinGW-w64, 64/32-bit, static/dynamic libs and executable. | https://github.com/curl/curl-for-win |
| OpenSSL for Solaris | Versions for Solaris 2.5 – 11 SPARC and X86 | http://www.unixpackages.com/ |
| OpensSSL for Windows, Linux, OSX, Android | Pre-compiled packages at conan.io package manager:Windows x86/x86_64 (Visual Studio 10, 12, 14, 15)Linux x86/x86_64 (gcc 4.6, 4.8, 4.9, 5, 6, 7)OSx (Apple clang).Cross-building ready recipe: Linux ARM, Android. | https://www.conan.io https://conan.io/center/openssl |
| OpenSSL for Windows | Pre-compiled Win32/64 1.0.2, 1.1.0, 1.1.1 and 3.0 libraries without external dependencies, primarily built for François Piette’s Internet Component Suite (ICS) for Embarcadero (Borland) Delphi and C++ development tools, but may be used for any Windows applications. The OpenSSL DLLs and EXE files are digitally code signed ‘Open Source Developer, François PIETTE’, so applications can self verify them for corruption. | http://wiki.overbyte.eu/wiki/index.php/ICS_Download |
| OpenSSL for Windows | OpenSSL 3.1, 3.0, and 1.1.1 pre-compiled for Microsoft Windows with no external dependencies. The binary distributions can be used standalone or integrated into any Windows application. Installer, EXEs and DLLs are digitally signed with ‘FireDaemon Technologies Limited’ Extended Validation (EV) code signing certificate. | https://www.firedaemon.com/get-openssl |
| OpenSSL for NonStop | Pre-compiled NonStop ia64/x86 1.0.2, 1.1.1 executables and libraries for the HPE NonStop Operating Systems. Threaded versions are included. The SPT version depends on FLOSS, otherwise there are no other dependencies. 32-bit versions are available. The builds are done by the ITUGLIB Technical Committee as part of Connect. | https://ituglib.connect-community.org/apps/Ituglib/SrchOpenSrcLib.xhtml |
How To Install OpenSSL On The Windows Platform?
The installation procedure is very simple and straightforward. Since OpenSSL does not provide official Windows installers, you need to download OpenSSL from trusted third-party sources listed on the OpenSSL Wiki.
We used Windows 11 64-bit and OpenSSL v 3.1.3 in this tutorial post.
Step 1. Download OpenSSL Installer
Visit any of the above sites and download the appropriate OpenSSL installer for your Windows version (32-bit or 64-bit). Make sure to pick the correct installer package for your machine.
Step 2. Run the OpenSSL Installer
Once downloaded, run the OpenSSL installer (.exe file) by double-clicking on it.
Accept the license agreement and choose the installation directory. The default is C:\Program Files\OpenSSL-Win64 but you can customize it.
The installer will copy all the required DLLs, and libraries, including files and executables. The installation typically finishes within a minute.
Step 3. Installation in progress…….
Step 4. Finish OpenSSL Installation
Once the installation completes, the setup wizard will prompt you to finish the installation. Click Finish to complete the OpenSSL installation process.
Step 5. Set Environment Variable
If you just want to set the environment varibles only for a login session, then run these commands.
>set OPENSSL_CONF=C:\Program Files\OpenSSL-Win64\bin\openssl.cfg
>set Path= C:\Program Files\OpenSSL-Win64\binIf you want to set the env variable for permanently, then add OPENSSL_CONF and Path environment variable on System Properties.
Open Run using ‘Windows’ + ‘r’ then type ‘sysdm.cpl‘. Go to Advanced > Environment Variable.
Set OPENSSL_CONF and Path variables.
Step 6. Verify the Installation
To verify that OpenSSL is installed correctly and added to PATH, open a new command prompt and run:
openssl versionThis will print the installed OpenSSL version and confirm the installation was successful.
You can also check all available commands by running:
openssl helpThis completes the installation of OpenSSL on Windows. You will see openssl.ext file in C:\Program Files\OpenSSL-Win64\bin directory.
Troubleshooting OpenSSL Issues
The real problem is not in installing OpenSSL on your Windows computer. The real problem encountered after the installation is when you start using OpenSSL. Many people reported that they were unable to run OpenSSL commands on their computers. This could be due to one of these reasons:
-
Incorrect environment variables – OpenSSL requires certain env vars like OPENSSL_CONF to be set properly. Not configuring these variables correctly can prevent things from working.
-
OpenSSL path not added – The OpenSSL install location needs to be added to the PATH env variable. Failing to do so will make the openssl command unrecognized.
-
Configuration issues – OpenSSL depends on its config file openssl.cnf. If this file is missing or corrupted, strange errors can occur.
-
Old OpenSSL version – OpenSSL releases new versions periodically with security fixes and improvements. Using an outdated OpenSSL can expose vulnerabilities. Upgrade to a newer version when possible.
-
Wrong architecture – Getting 32-bit and 64-bit versions mixed up can lead to errors. Make sure to install the version that matches your Windows architecture.
-
Missing DLL files – OpenSSL relies on certain DLL files like libeay32.dll and ssleay32.dll. If these files are missing or not in the system path, OpenSSL commands will fail.
The first thing you should do is to download the correct installer file and reinstall the OpenSSL. This solves problems like missing DLL and wrong architecture. Generally, version-related issues were seen least oftentimes. You can try fixing version-related issues by reinstalling a different version.
If your problem still persists, then the reason could either be with environment variables or OpenSSL configuration files. Let’s try to troubleshoot.
You should start troubleshooting by running openssl version command. If you get any error, ensure you configured OPENSSL_CONF and Path environment variable as per step 5. We should tell you about the two prominent configuration files openssl.cfg and openssl.cnf. People often get confused with these files. Just pay attention to the extensions .cfg and .cnf. You should set the environment variable OPENSSL_CONF to openssl.cfg file.
Let’s understand openssl.cfg and openssl.cnf configuration files in OpenSSL.
-
openssl.cfg – This is the default configuration file that comes with OpenSSL. It contains default settings for OpenSSL when no other config file is specified. The openssl.cfg file is located in the apps subfolder of the OpenSSL install directory.
-
openssl.cnf – This is the recommended main configuration file for OpenSSL. It contains sections for settings like certificate authority locations, certificate policies, default algorithms and protocols etc. The openssl.cnf file allows extensive customization of OpenSSL behavior.
It may sound similar. Let’s see the difference between to know more about these two files.
The main differences between openssl.cfg and openssl.cnf are:
-
openssl.cfg contains minimal default settings just to get OpenSSL working out of the box. openssl.cnf has extensive options to control OpenSSL behavior.
-
openssl.cfg is automatically loaded if no other config is specified. openssl.cnf must be explicitly specified using the -config option.
-
openssl.cfg is limited and intended for initial testing. openssl.cnf is meant for production use and customization.
-
openssl.cfg sets insecure default settings like using MD5 hashes. openssl.cnf has more conservative secure defaults.
-
Anything set in openssl.cnf will override the defaults in openssl.cfg. openssl.cnf is treated as the main config.
In Windows, openssl.cfg file is located at C:\Program Files\OpenSSL-Win64\bin directory. The openssl.cnf file is located at two locations: C:\Program Files\Common Files\SSL and C:\Program Files\OpenSSL-Win64\bin\cnf.
If you get an error messages “Can’t open /usr/lib/ssl/openssl.cnf for reading, No such file or directory” and “cannot access ‘/etc/ssl/openssl.cnf’: No such file or directory“. Make sure you have both files in their path and that environment variables are set.
If in case your openssl.cnf file is missing or unable to see, you can download openssl.cnf file from MIT (Massachusetts Institute of Technology). MIT provides a generic configuration file that you can use. You can download the file to these directories to fix the errors.
-
C:\Program Files\Common Files\SSL\
-
C:\Program Files\OpenSSL-Win64\bin\cnf\
If you set all these things, you are not going to see any issues in OpenSSL.
Bottom Line
Installing OpenSSL on Windows provides access to a robust cryptographic toolkit for secure communication and certificate management. This step-by-step guide covered downloading OpenSSL installers from the trusted third-party distributors, installing it on a Windows machine, setting up environment variables, and verifying the installation.
With OpenSSL added to your Windows desktop or server, you can now generate public/private key pairs, create and manage X.509 certificates, test SSL/TLS connections, implement encryption in your apps, and much more.
We hope this step-by-step procedure helps understand everything about the instillation of OpenSSL on a Windows machine. Thanks for reading this post. Please share this post and help secure the digital world. Visit our website, thesecmaster.com, and our social media page on Facebook, LinkedIn, Twitter, Telegram, Tumblr, Medium, and Instagram and subscribe to receive updates like this.
You may also like these articles:
Arun KL
Arun KL is a cybersecurity professional with 15+ years of experience in IT infrastructure, cloud security, vulnerability management, Penetration Testing, security operations, and incident response. He is adept at designing and implementing robust security solutions to safeguard systems and data. Arun holds multiple industry certifications including CCNA, CCNA Security, RHCE, CEH, and AWS Security.
Generating SSL certificates can be a daunting task, one filled with frustration and sorrow. But it doesn’t have to be that way! If you have Windows 10 and OpenSSL along with a little help from this tutorial, you will be well on your way.
Not a reader? Watch this related video tutorial!
Not seeing the video? Make sure your ad blocker is disabled.
In this article, you’re going to learn how to install OpenSSL on Windows 10. Once installed, you’ll then generate SSL certificates, troubleshoot and debug certificates, and convert between formats.
Let’s begin mastering OpenSSL on Windows 10 with PowerShell!
Related: Managing Certs with Windows Certificate Manager and PowerShell
Prerequisites
In this article, you are going to learn using a hands-on approach. While OpenSSL historically is a Linux OS utility, you can use it with Windows OS as well.
- A Windows system with Local Administrator rights – The tutorial will be using Windows 10
- Windows PowerShell 5.1 (comes with Windows) or PowerShell 7
- Chocolatey – A package manager for Windows installed.
- PowerShell ISE, Visual Studio Code or any text editor of your choice
All screenshots in this guide were taken from Windows 10 build 1909 and PowerShell 7.
Installing OpenSSL on Windows 10 with PowerShell and Chocolatey
Assuming you have installed Chocolatey using the installation instructions, your first task is to install OpenSSL on Windows 10. To do this, open up your PowerShell console and run choco install OpenSSL.Lightas shown below.
That’s it! You’ve now installed OpenSSL with PowerShell.
Set up a Working Directory
This tutorial will be creating a few certificates to learn from. To ensure all of the work you do here is confined to a single folder you can clean up later, go ahead and create one.
This tutorial will store all certificates and related files in the C:\certs folder. You can create a folder with PowerShell by running the below command.
New-Item -ItemType Directory -Path C:\certsNow it’s time to configure OpenSSL.
Configuring OpenSSL
By default, OpenSSL on Windows 10 does not come with a configuration file. This is intentional because there are a lot of configuration options that you can customize. For the purposes of this guide, you are going to use a sample configuration that you can customize later to best suit your security requirements.
Open up PowerShell and run the below command. This command downloads a sample configuration file from MIT and saves it as openssl.cnf in the current working directory.
You can now open up the openssl.cnf file and you should see something that looks like below.
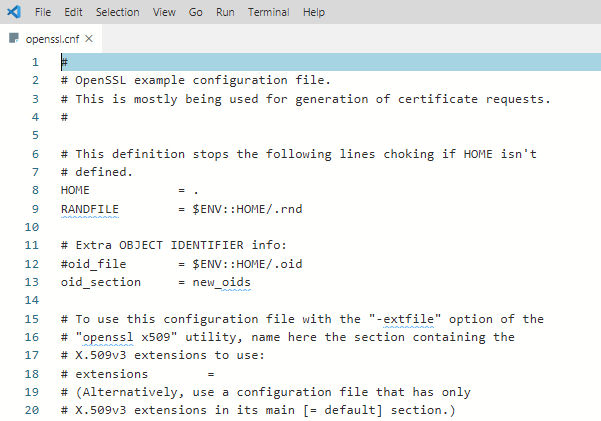
The downloaded configuration will work as-is for now. Do not use the defaults in a production environment!
Update PowerShell Profile Environment Variables
To make things go smoothly, you should modify your PowerShell profile on Windows 10. Setting up some environment variables allows you to easily switch between different versions of OpenSSL that you may have installed.
I suggest adding two environment variables to your PowerShell profile called path and OPENSSL_CONF. You will update the PATH environment variable to ensure you can run the openssl binary in any location while on the command line.
Below you’ll see a way to create a PowerShell profile if you don’t already have one. This command appends the OpenSSL binary path to your PATH and assign the configuration file path to OPENSSL_CONF.
# Add environment variables to PowerShell profile
# Test for a profile, if not found create one!
if (-not (Test-Path $profile) ) {
New-Item -Path $profile -ItemType File -Force
}
# Edit profile to add these lines
'$env:path = "$env:path;C:\Program Files\OpenSSL\bin"' | Out-File $profile -Append
'$env:OPENSSL_CONF = "C:\certs\openssl.cnf"' | Out-File $profile -AppendTo use the environment variables, reload your profile typing . $profile or just close and reopen PowerShell.
Now you can easily invoke the openssl binary wherever you are in PowerShell as shown below.

Using OpenSSL on Windows 10 to Generate a CSR & Private Key
Before you can create an SSL certificate, you must generate a certifiate-signing request (CSR). A CSR is an encoded file that provides you with a way to share your public key with a certificate authority (CA). This file contains identifying information, a signature algorithm, and a digital signature. Let’s create your first CSR and private key.
Related: Understanding X509 Certificates: A Clear and Concise Guide (For Mortals)
To create a CSR, run the below command. OpenSSL will then prompt you to enter some identifying information as you can see in the following demonstration.
openssl req -new -out MyFirst.csr
Once complete, you will have a valid CSR and private key which can be used to issue an SSL certificate to you.
The configuration file defaults can be edited further to streamline this process should you not want to enter data every time you generate a CSR.
You can read more about the available CSR options and view sample configurations in the man pages. OpenSSL also has an active GitHub repository with examples too.
Generating RSA Key Pairs
You can also create RSA key pairs (public/private) with OpenSSL. To do so, first, create a private key using the genrsa sub-command as shown below.
When you run the command below, OpenSSL on Windows 10 will generate a RSA private key with a key length of 2048 bits. This key is generated almost immediately on modern hardware. The resulting key is output in the working directory
# generate a private key using maximum key size of 2048
# key sizes can be 512, 758, 1024, 1536 or 2048.
openssl genrsa -out rsa.private 2048Next, generate a public key using the private key that you just created using the rsa sub-command. The syntax below will create a public key called rsa.public in the working directory from the rsa.private private key.
# generate a public key using the private key
openssl rsa -in rsa.private -out rsa.public -pubout -outform PEMGenerating a Self-Signed Certificate
On occasion you may need to generate a self-signed certificate. Self-signed certificates are fine to use for lab use but not a secure practice to use in a production environment.
Let’s create a self-signed certificate before moving onto the next task. To do so, enter the command below to create an X509 SSL certificate. This certificate will use SHA256 cryptography that will be valid for 365 days using an RSA key length of 2048 bits. The certificate will be saved to the working directory.
openssl req -x509 -sha256 -nodes -days 365 -newkey rsa:2048 -keyout privateKey.key -out certificate.crtYou are now ready to import the certificate into a browser or server.
Validating CSRs, Certificates, and Keys with OpenSSL
Checking the information in a CSR, private key, certificate, or PKCS#12 can save you time troubleshooting SSL errors. Sometimes a wrong key may have been used to create a certificate, for example. You may have the wrong identifying information in the certificate.
Let’s start by checking a CSR using the req command and some parameters:
openssl req -text -noout -verify -in .\MyFirst.csr
Details such as country name, organizational name, and the email address you entered when creating the CSR at the beginning of this guide, should match precisely.
You can also check a certificate using the x509 sub-command with a couple of parameters:
openssl x509 -in .\certificate.crt -text -noout | more
Converting Certificates with OpenSSL
There are occasions where an application does not use a particular certificate format. You can run into this issue with an application called HAproxy, for example that requires a PEM certificate when you may have a DER-formatted certificate (.crt .cer .der).
To demonstrate converting a certificate, let’s convert the self-signed certificate created earlier in a DER format (certificate.crt) to PEM. Use the code in the following code snippet to do so.
This command below uses the x509 sub-command with the parameter of -inform which should match the format of the -in file followed by the -out format.
openssl x509 -inform der -in .\certificate.crt -out .\certificate.pemYou can also reverse the order if you’d like to the DER format from PEM too as shown below.
openssl x509 -outform der -in .\certificate.pem -out .\certificate.derAnd last but not least, you can convert PKCS#12 to PEM and PEM to PKCS#12. This is a file type that contain private keys and certificates. To convert to PEM format, use the pkcs12 sub-command.
openssl pkcs12 -in .\SomeKeyStore.pfx -out .\SomeKeyStore.pem -nodesYou can convert a PEM certificate and private key to PKCS#12 format as well using -export with a few additional options. Below you are exporting a PKCS#12 formatted certificate using your private key by using SomeCertificate.crt as the input source. Using the -certfile option value MyCACert.crt allows you to validate SomeCertificate.crt.
openssl pkcs12 -export -out SomeCertificate.pfx -inkey SomePrivateKey.key -in SomeCertificate.crt -certfile MyCACert.crtTroubleshooting & Debugging
Now that you can create & convert CSR’s, certificates, and key pairs, it’s time to learn how to troubleshoot and debug them. OpenSSL comes with commands that make it a breeze to troubleshoot problems.
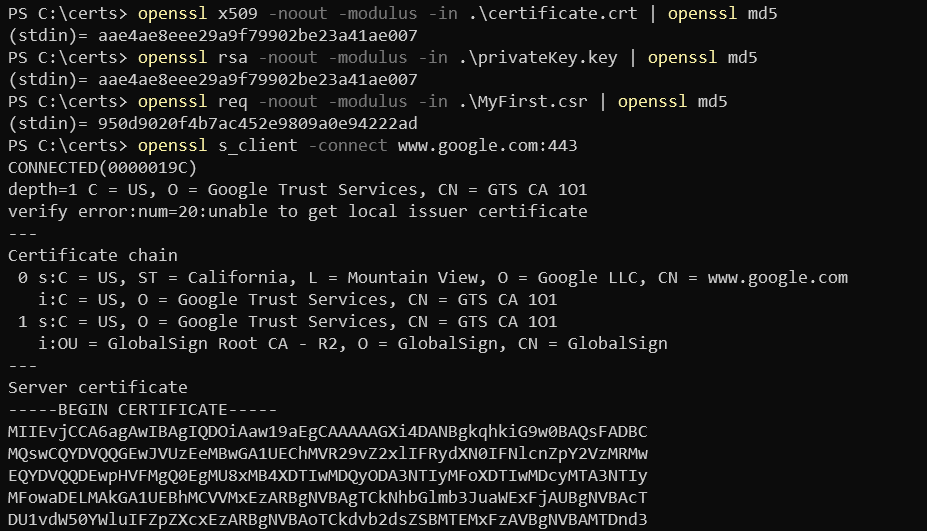
OpenSSL also allows you to check certificates for file integrity and test for possible data corruption. Using an MD5 checksum, you can use the following code examples to test certificates, keys and CSR’s:
# Certificates
openssl x509 -noout -modulus -in .\certificate.crt | openssl md5
# Public / Private Keys
openssl rsa -noout -modulus -in .\privateKey.key | openssl md5
# Certificate Server Request
openssl req -noout -modulus -in .\MyFirst.csr | openssl md5
# Check an external SSL connection
openssl s_client -connect www.google.com:443Once you have the original hash, you can then compare that original hash with a current hash to verify the certificate hasn’t been modified or corrupted.
Here’s a sample of what that code looks like when run in PowerShell:
Summary
In this article, you have learned how to install and configure OpenSSL on Windows 10, create a CSR, key pair, and SSL certificate. You have also learned how to convert between different certificate formats and do some basic troubleshooting using built-in sub-commands.
Additional Resources
- OpenSSL config man page
- OpenSSL commands
- Online SSL Checker
- Automating IIS SSL Certificate Installation with PowerShell
- How to Create Self-Signed Certificates with PowerShell
Provide feedback
Saved searches
Use saved searches to filter your results more quickly
Sign up
